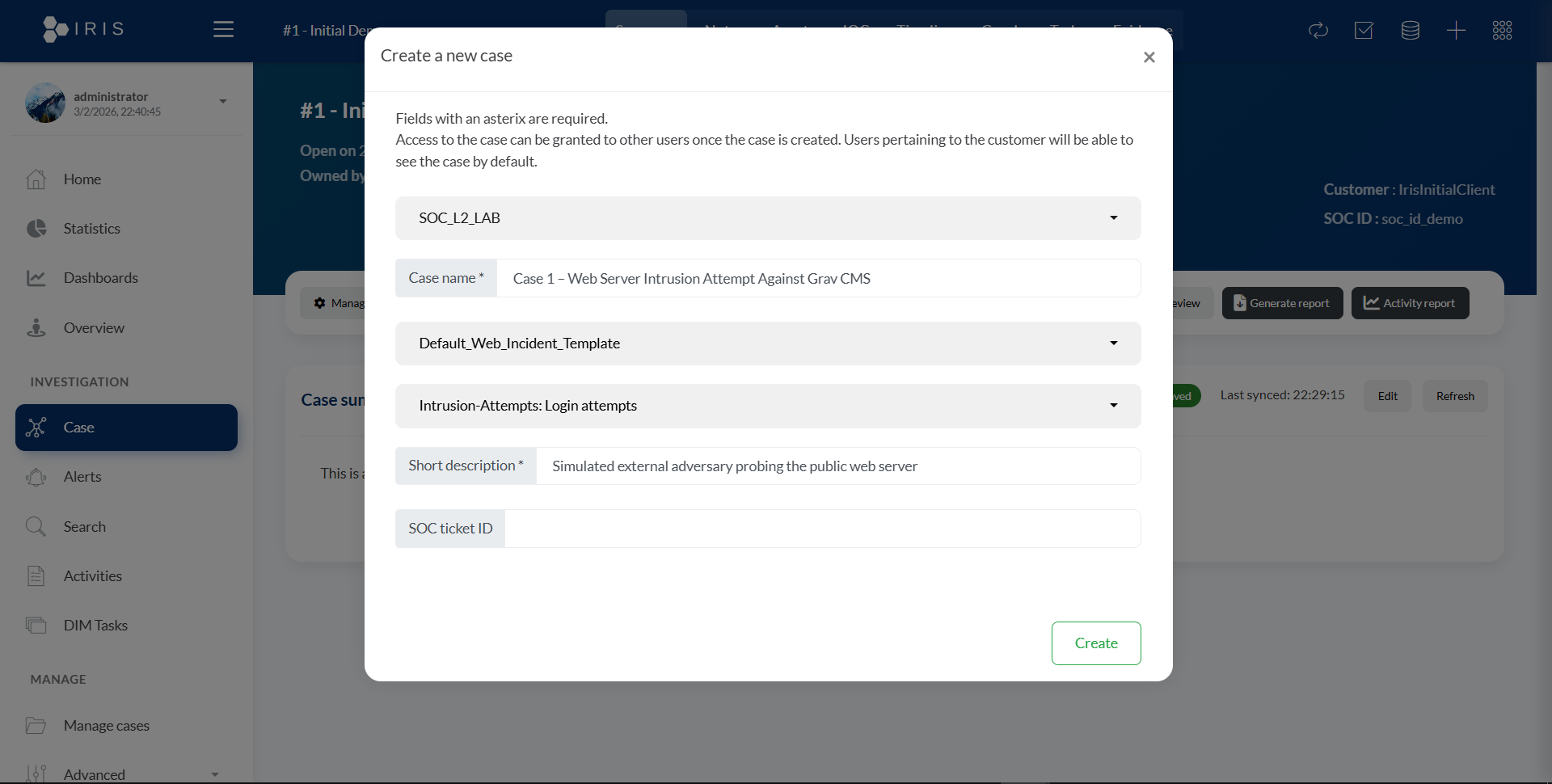
This case simulates an attacker probing a Linux web server running Grav CMS. The investigation includes attacker activity (Kali), SIEM visibility (Wazuh), and incident response workflow (DFIR‑IRIS).
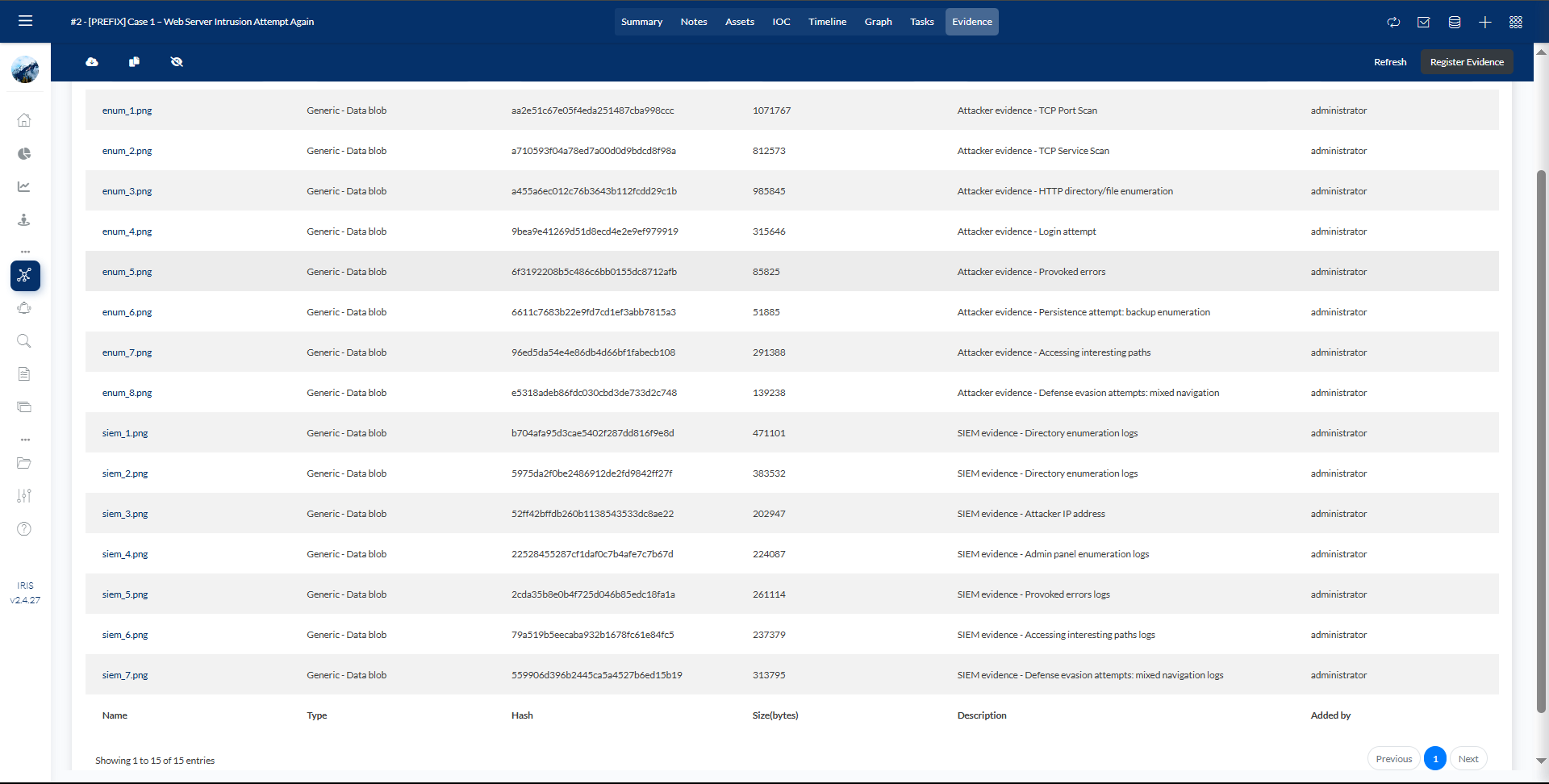
Summary of attacker actions performed from Kali.
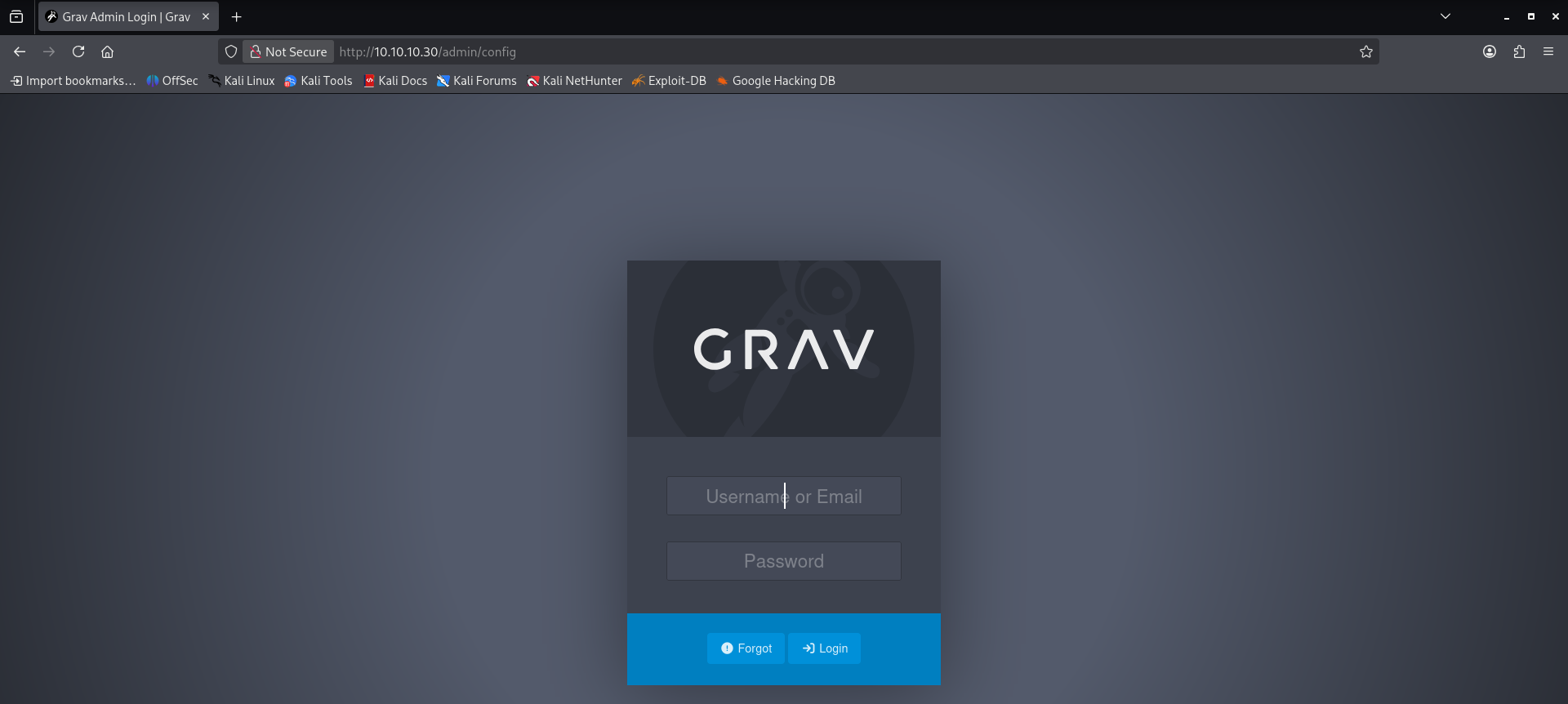
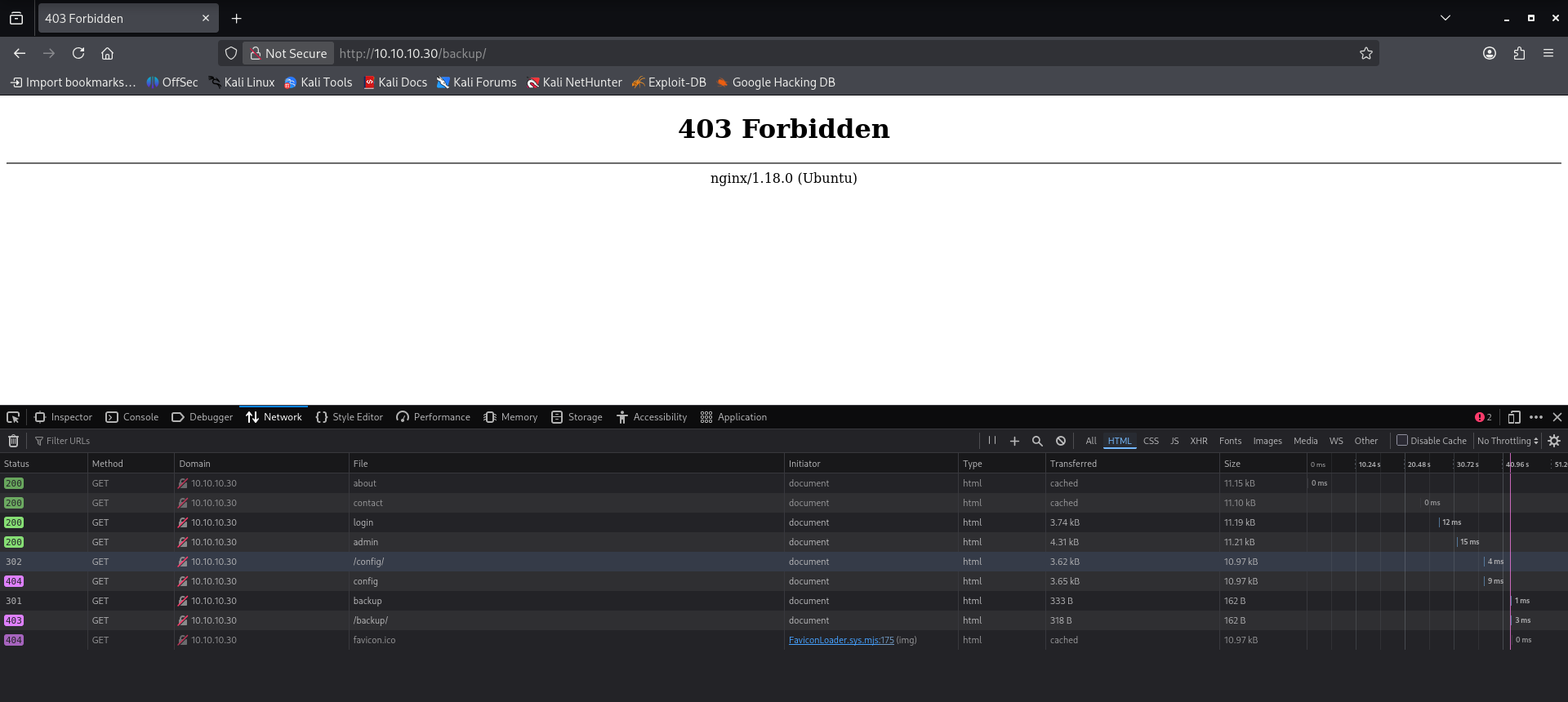
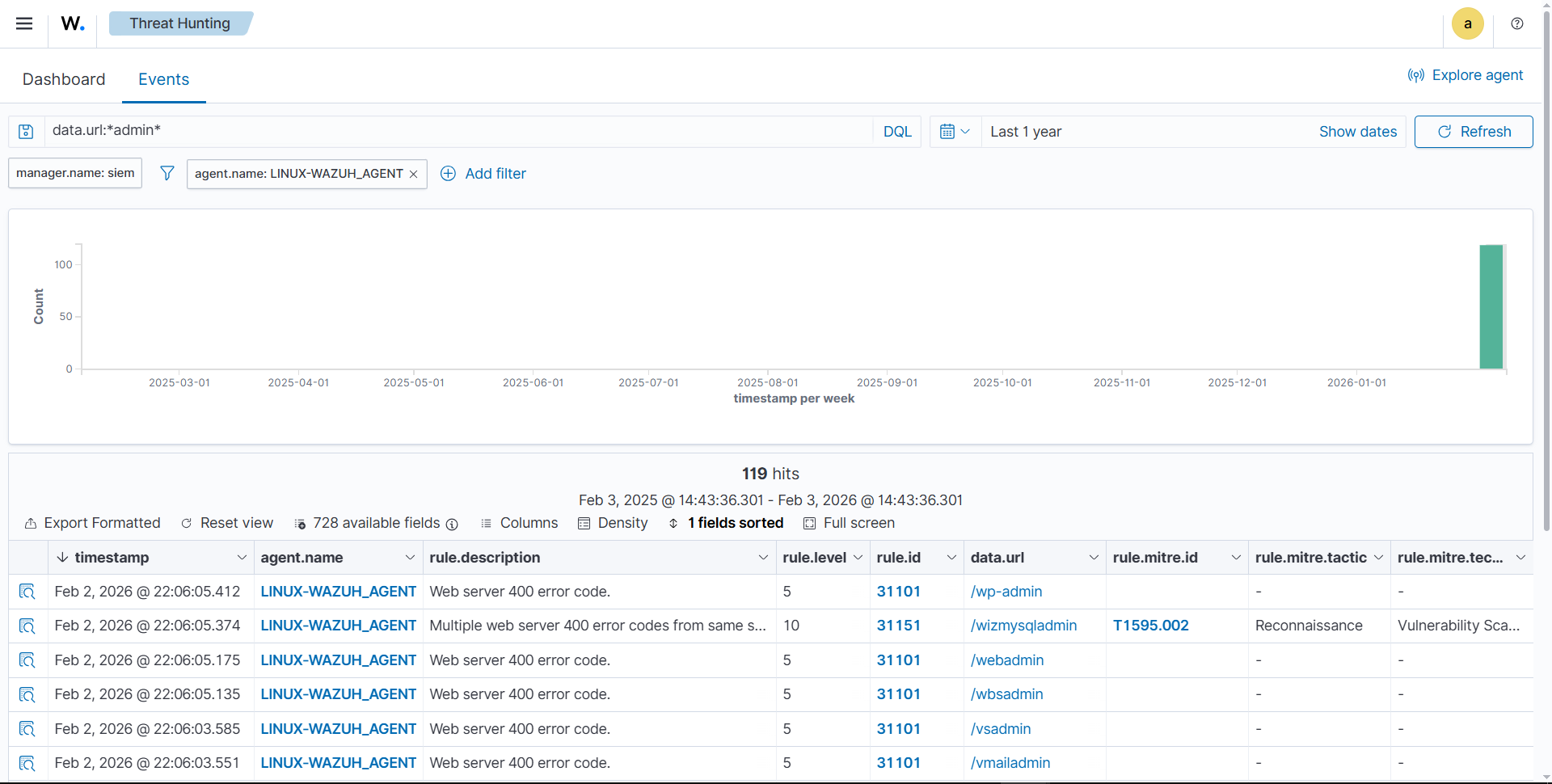
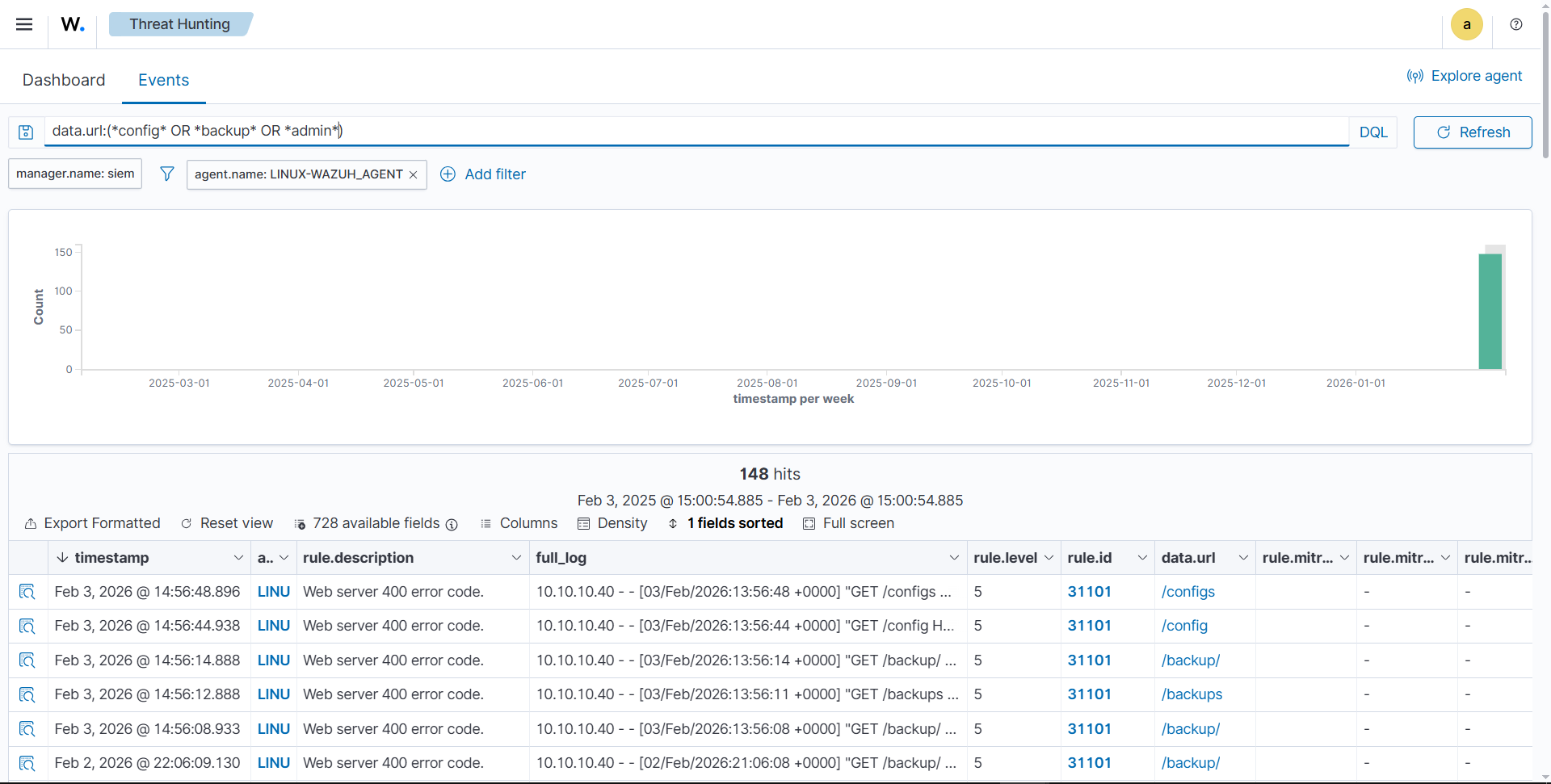
Webserver scan and enumeration.
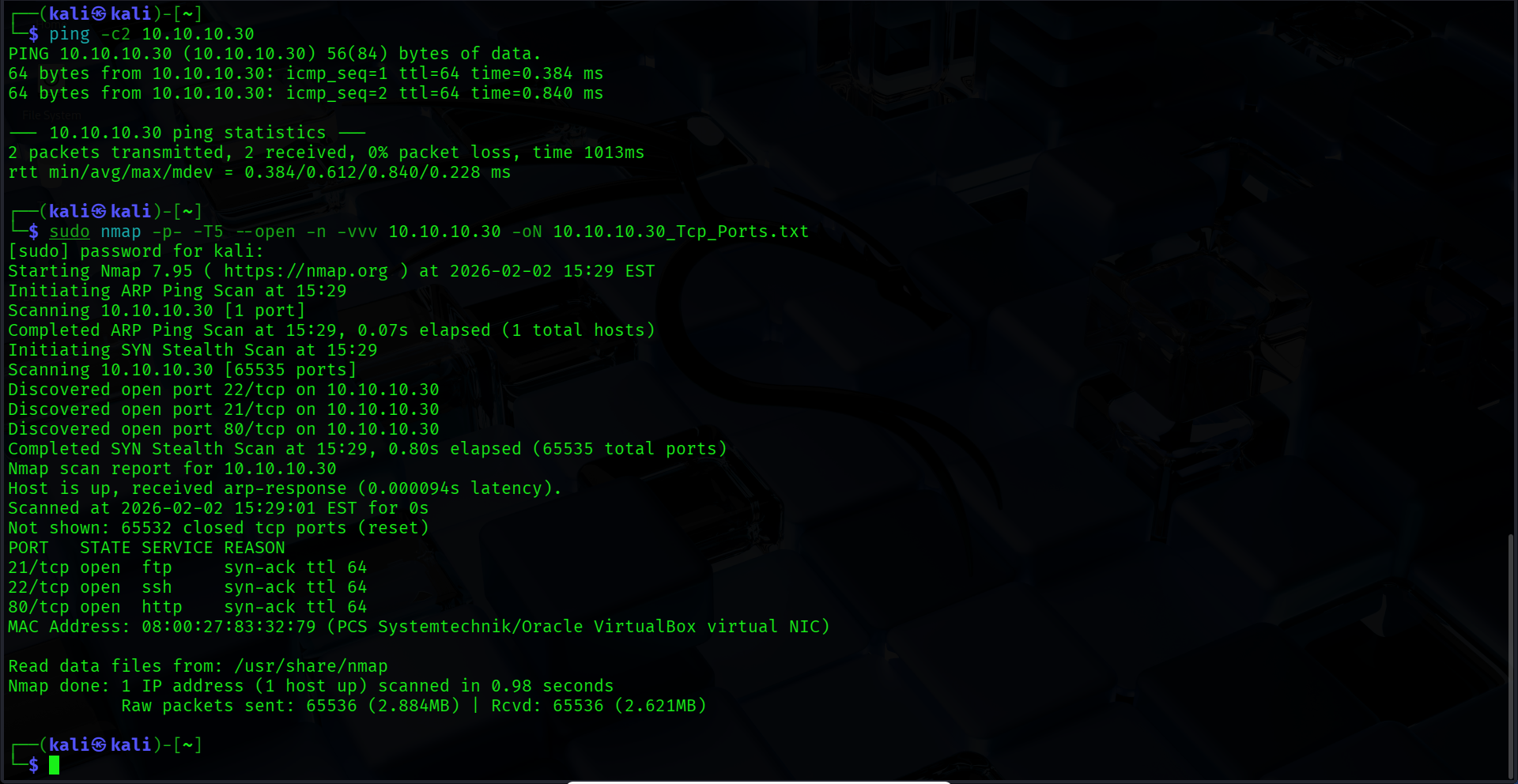
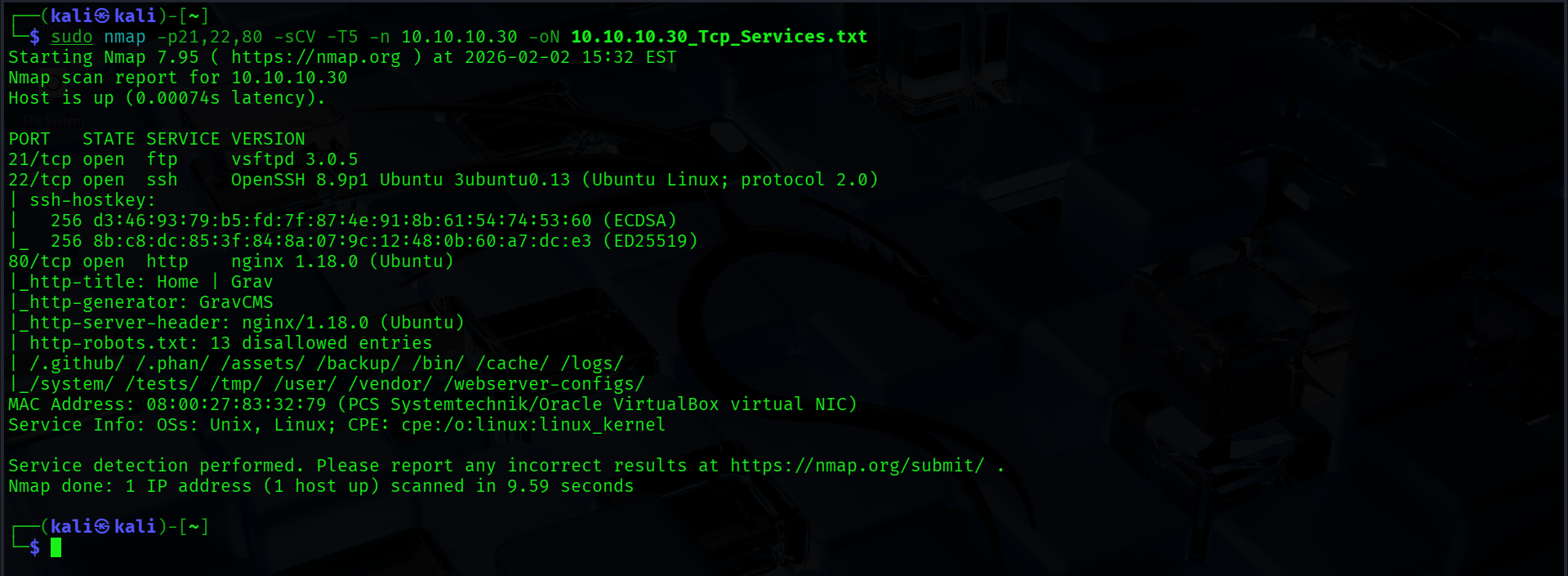
dirb http://10.10.10.30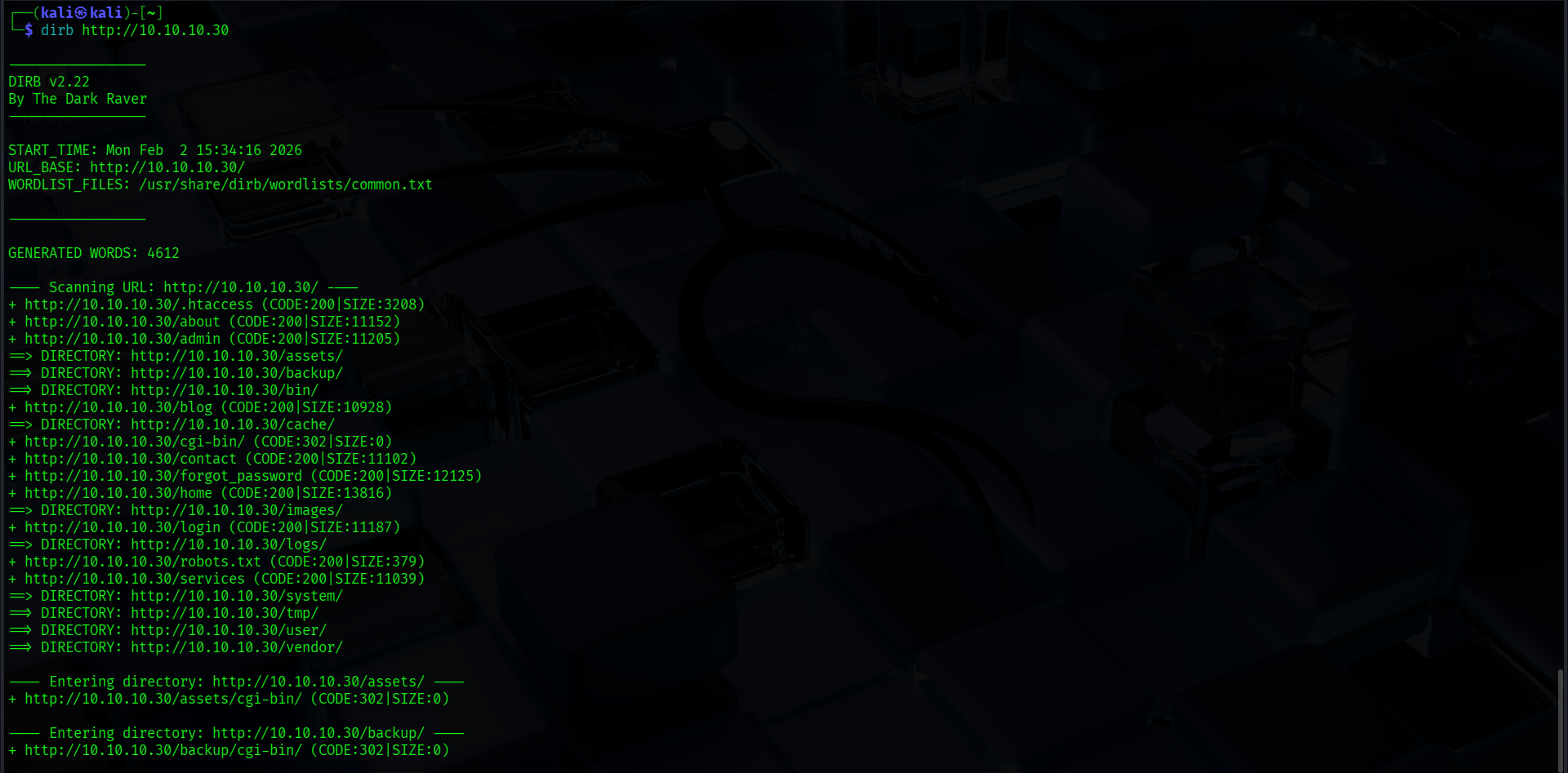
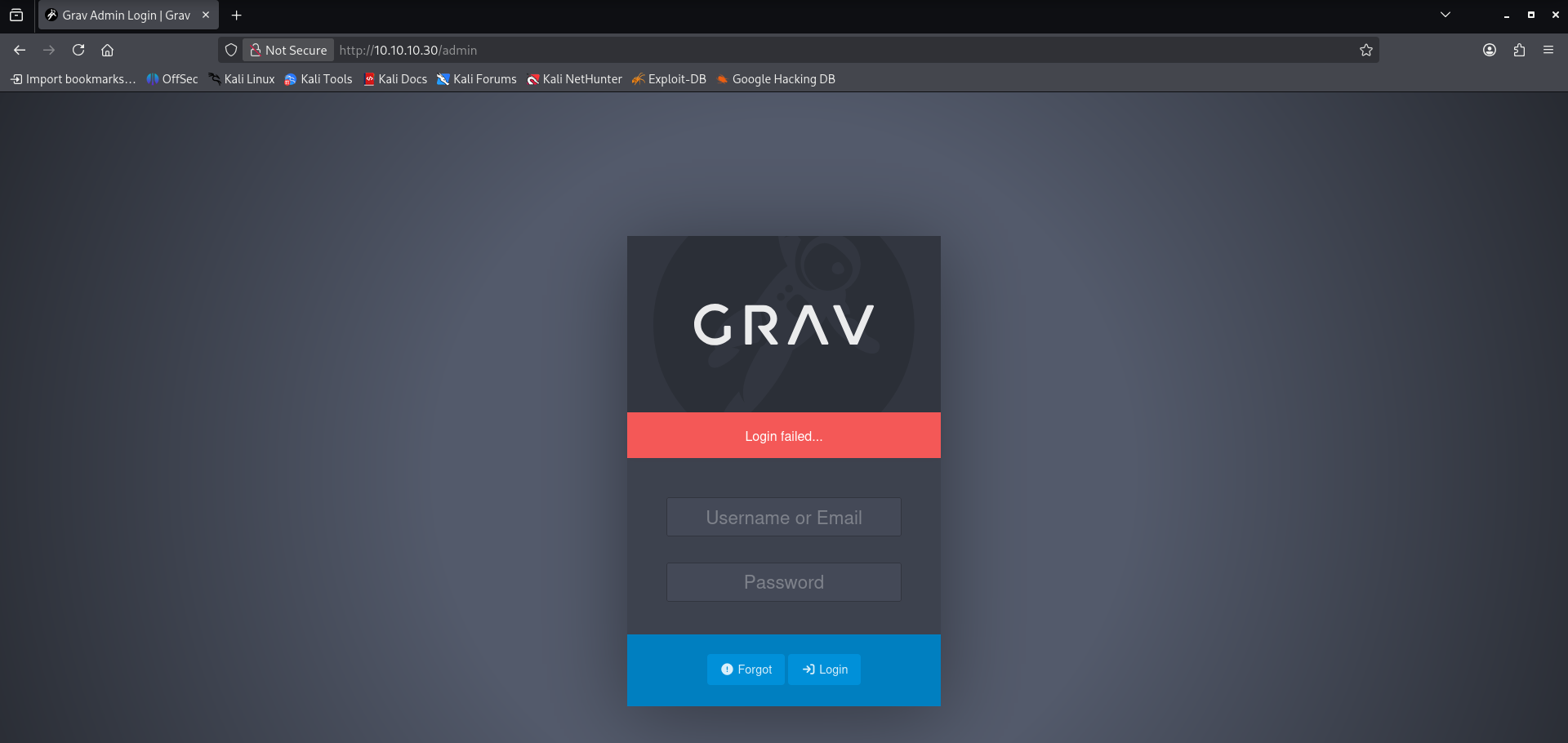
Weak credentials and error generation.
admin:admin
test:test
user:user
etc.
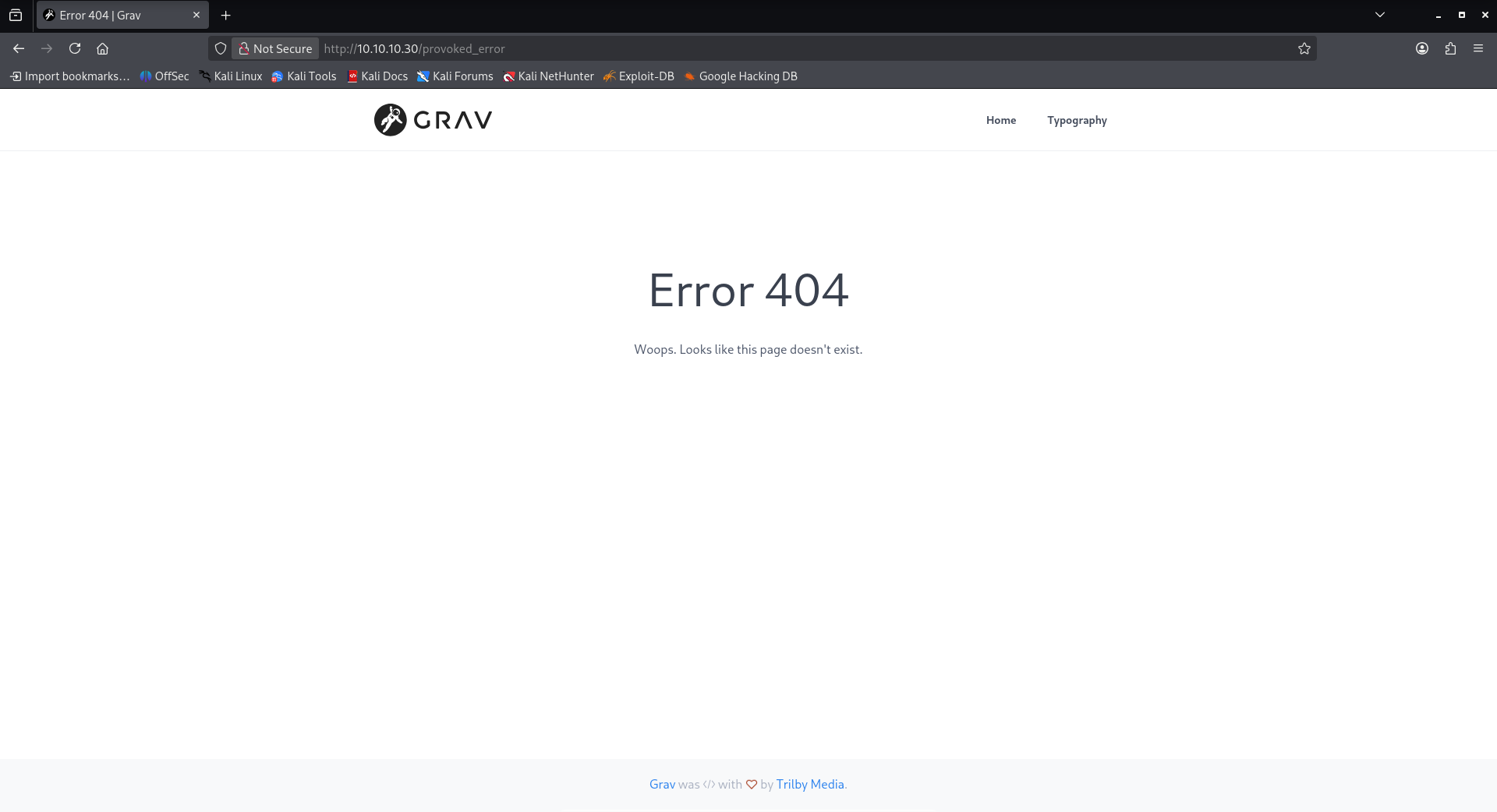
Accessing restricted or interesting paths.
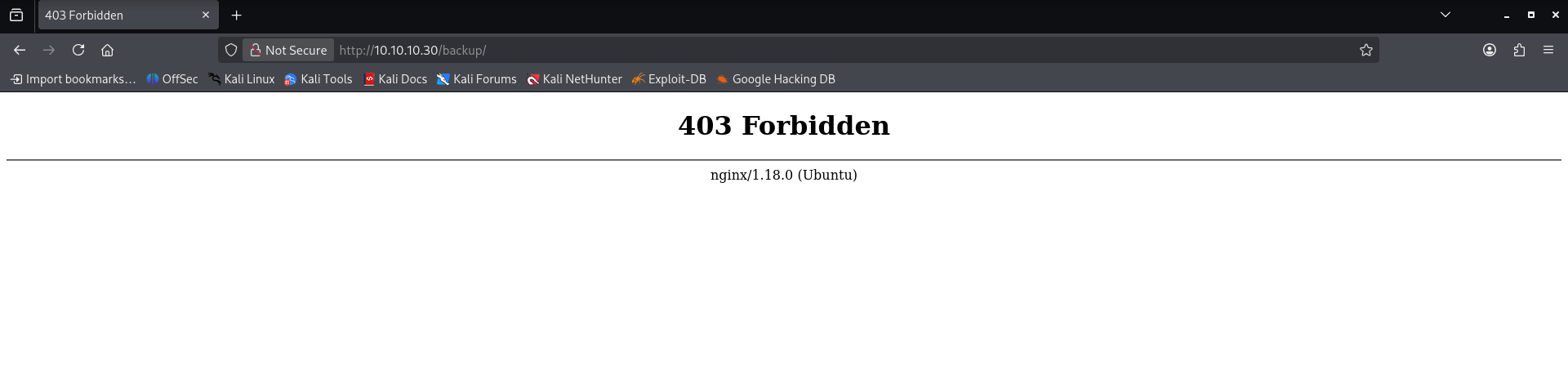
Mixed navigation and varying patterns.
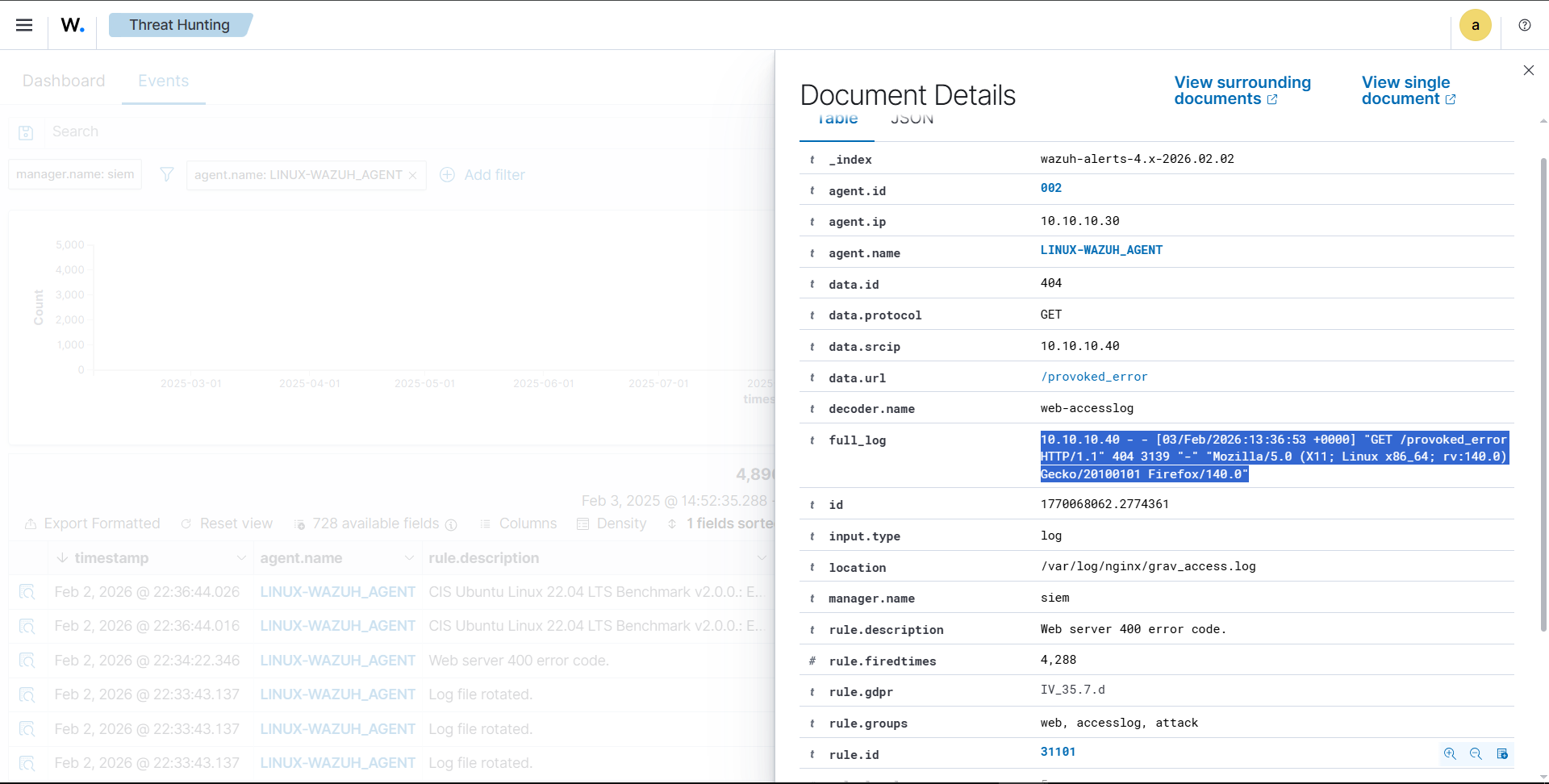
How Wazuh detected and logged the activity.
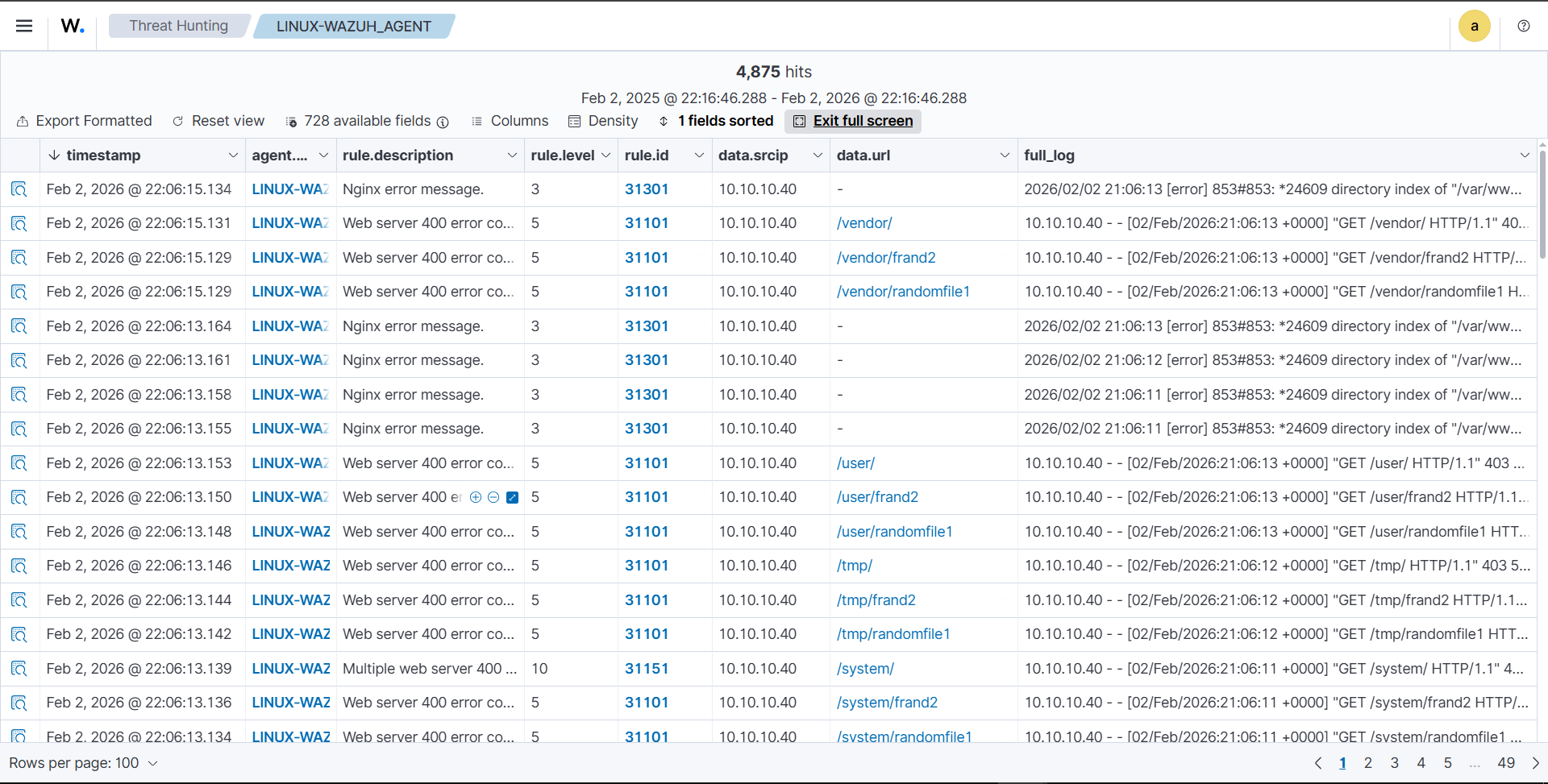
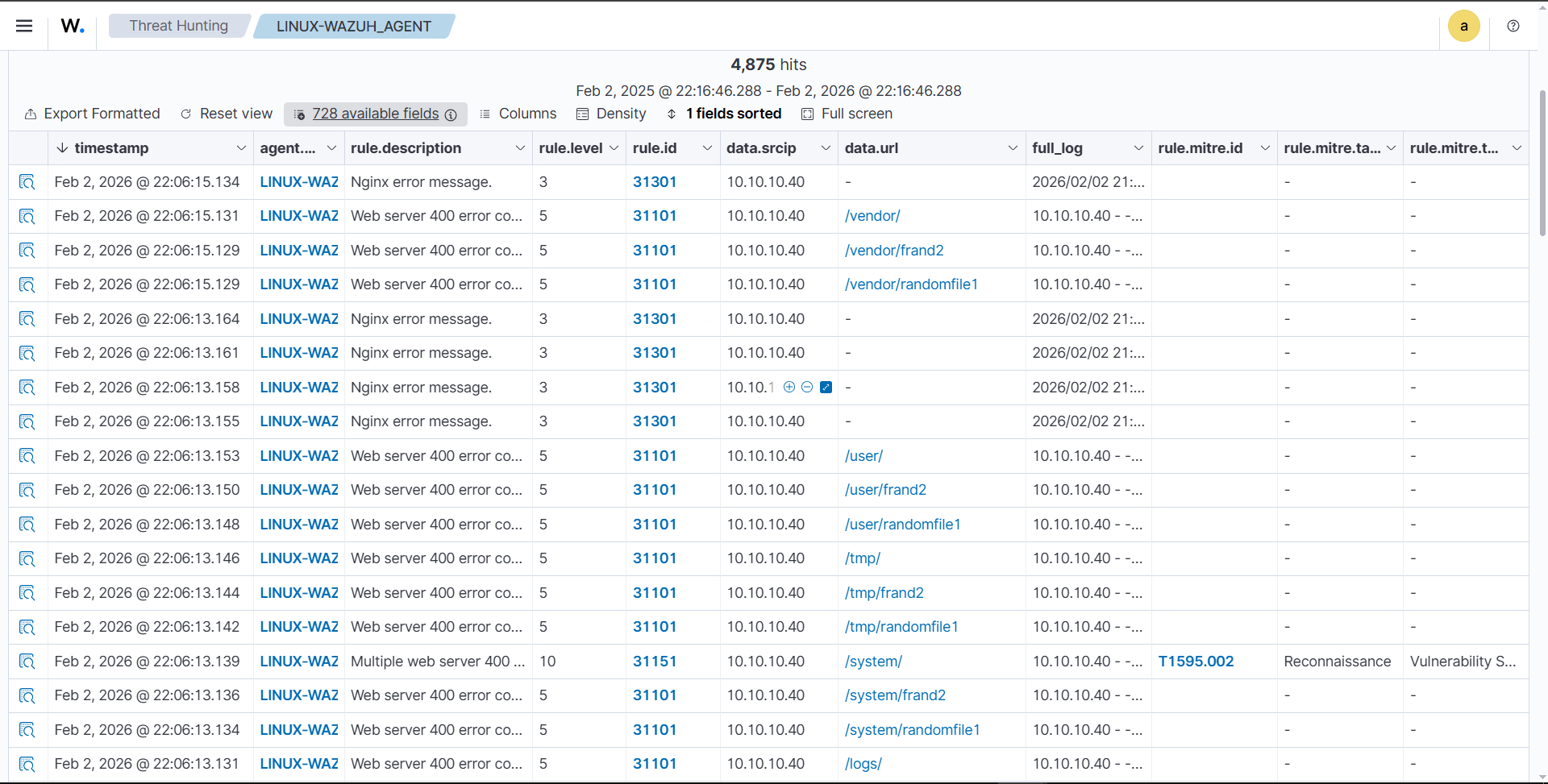
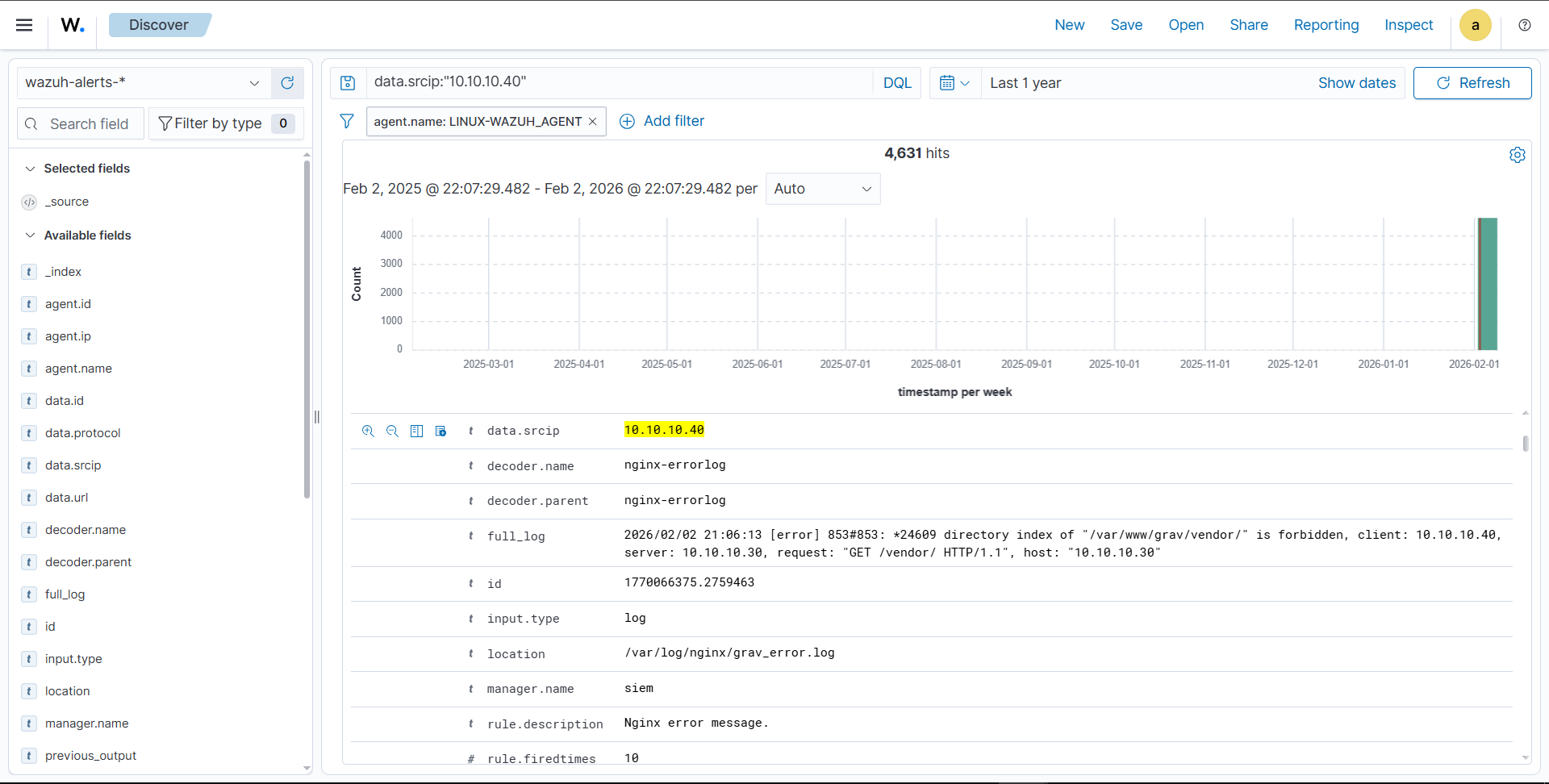
Access logs and error logs.
10.10.10.40 - - [03/Feb/2026:13:36:53 +0000] "GET /provoked_error HTTP/1.1" 404 3139 "-" "Mozilla/5.0 (X11; Linux x86_64; rv:140.0 Gecko/20100101 Firefox/140.0")
How alerts tie together into a single incident, including mixed navigation.
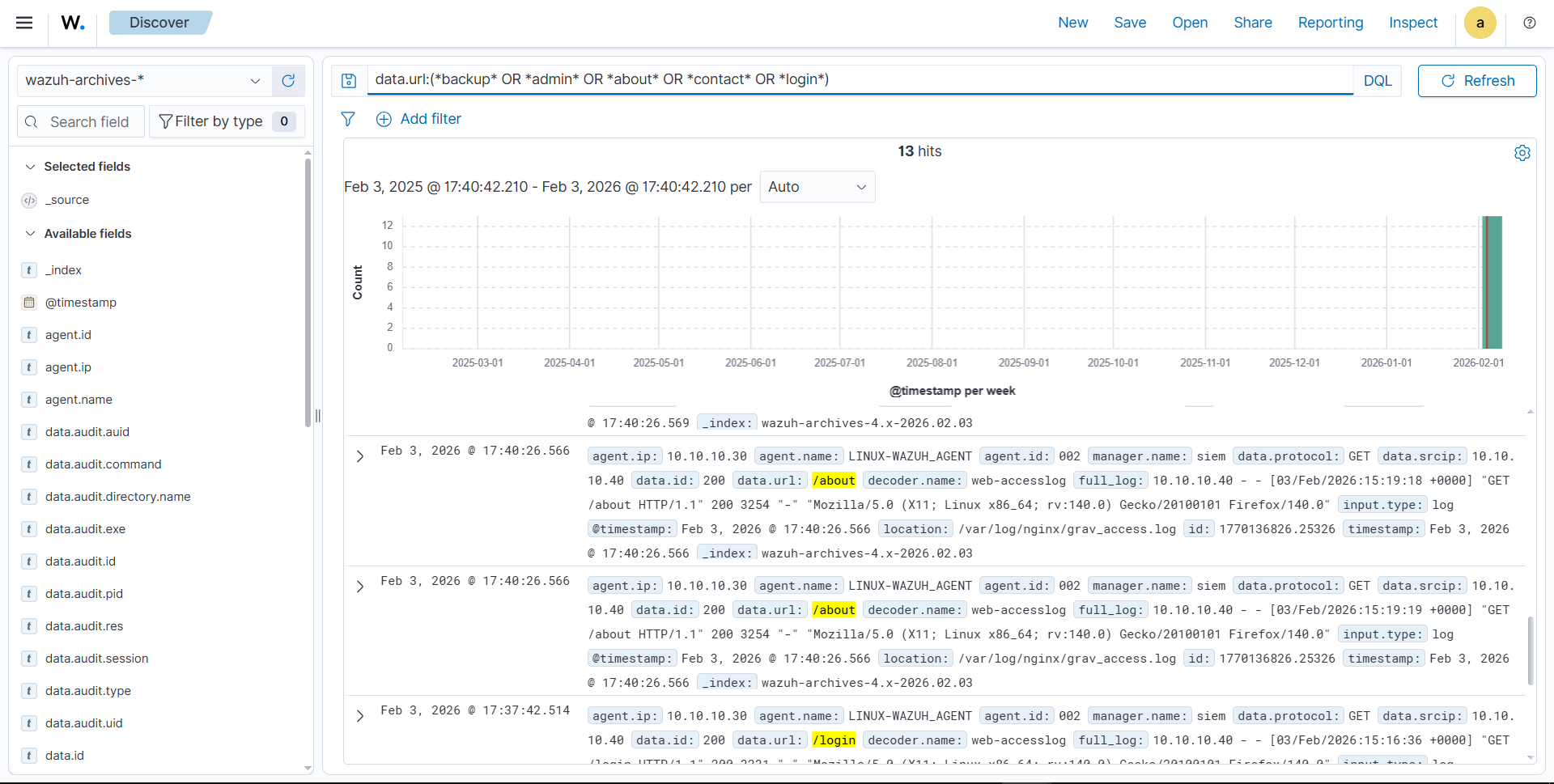
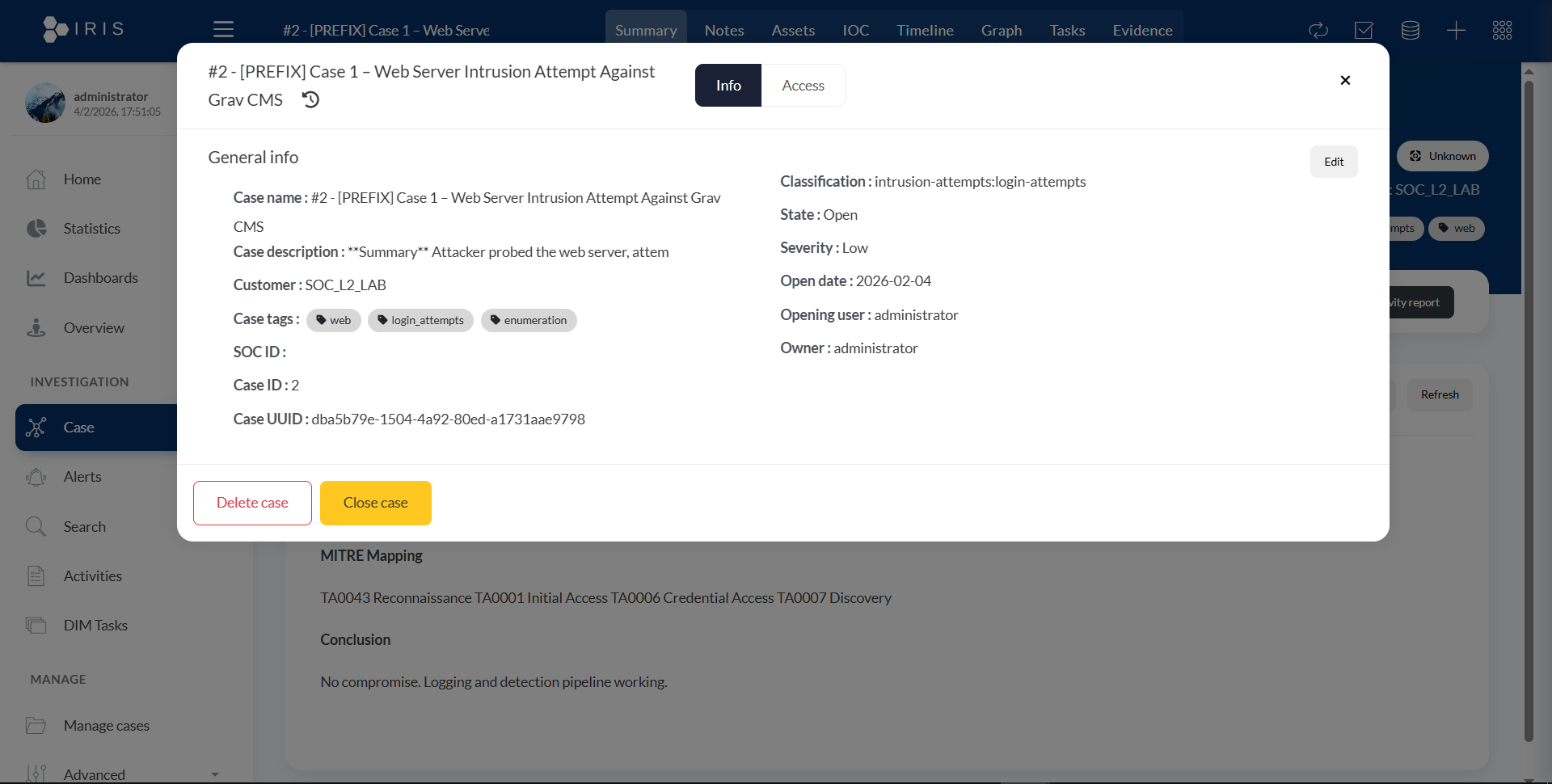
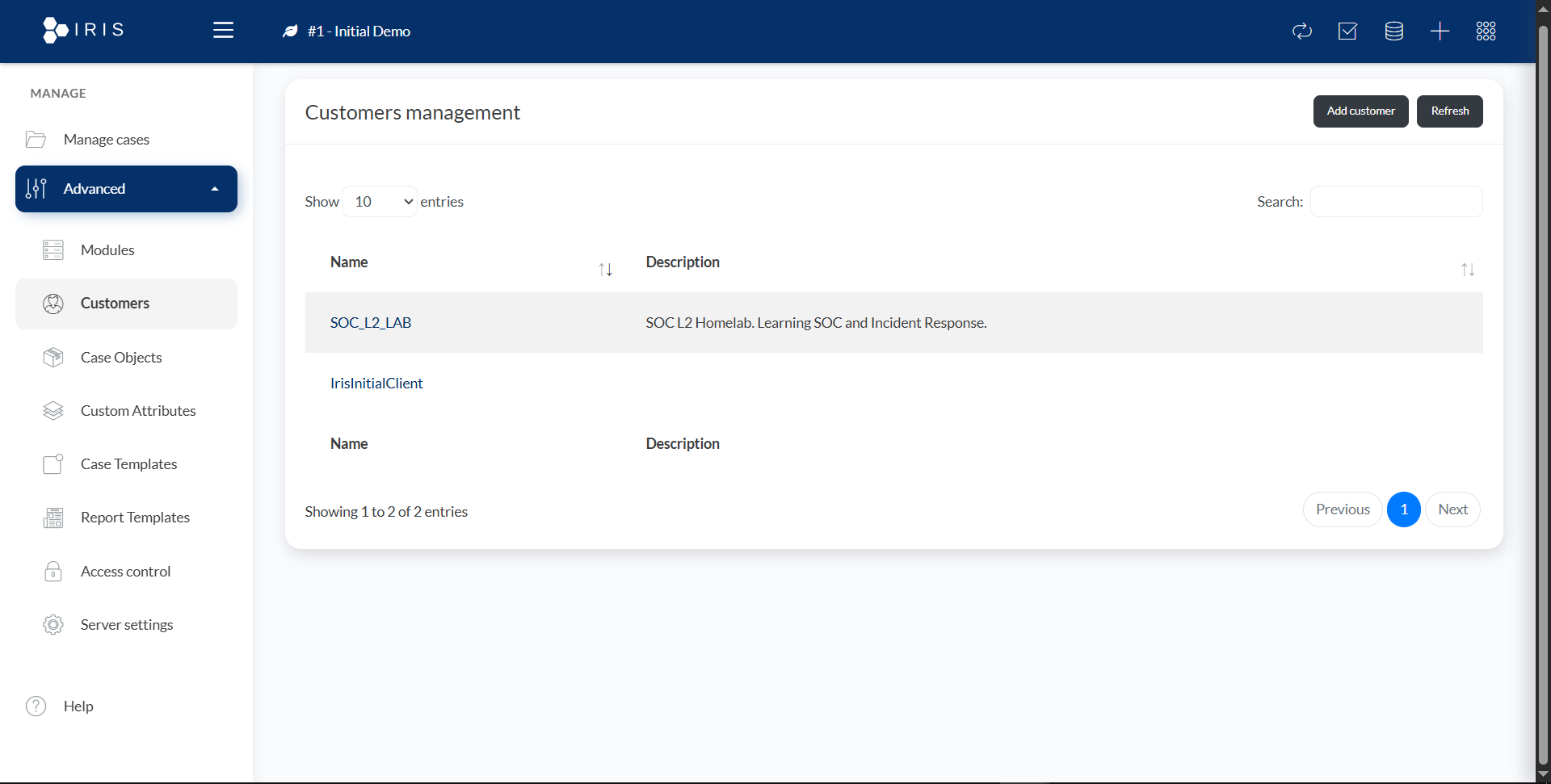
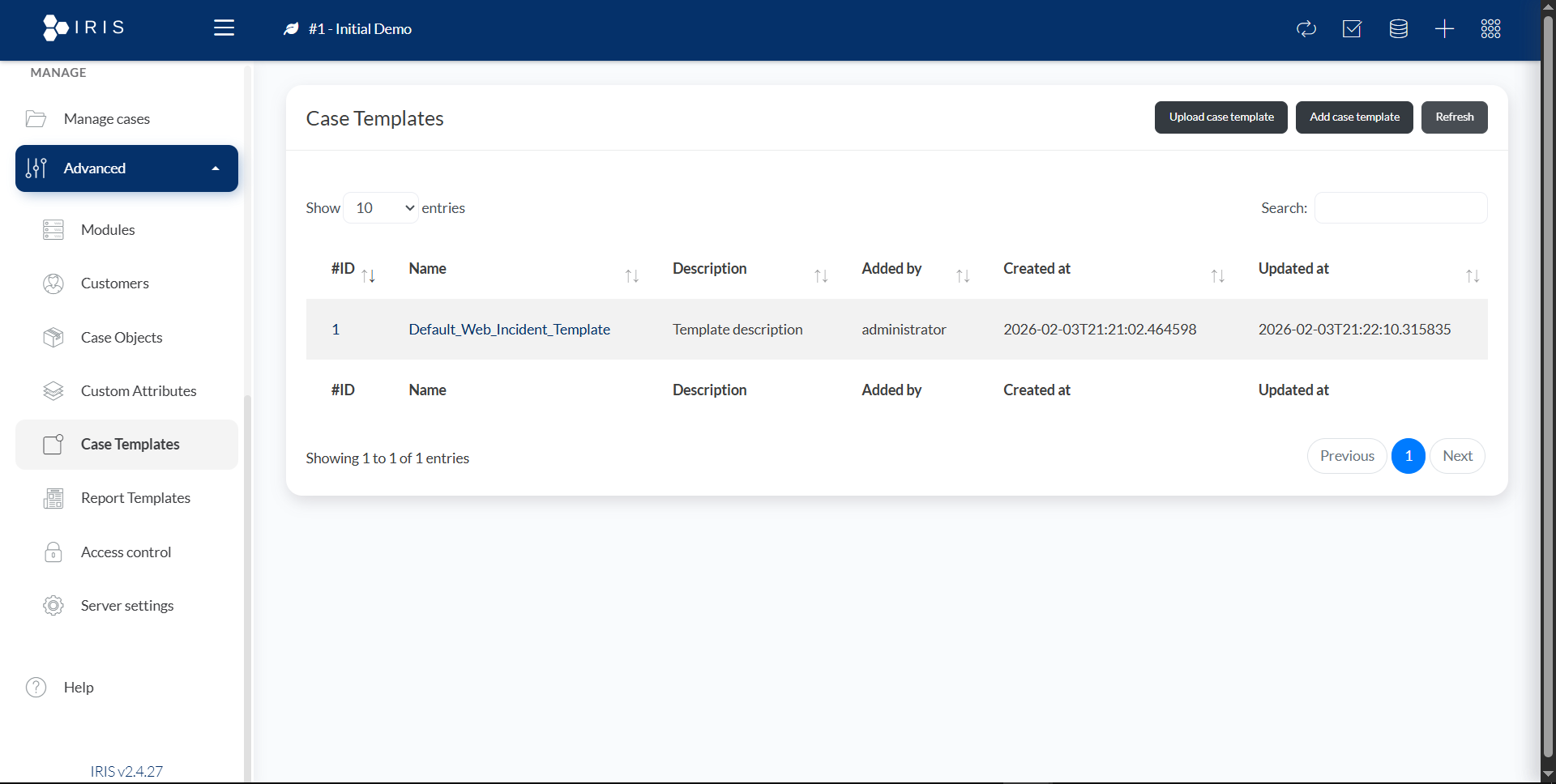
How the case was documented and analyzed in DFIR‑IRIS.
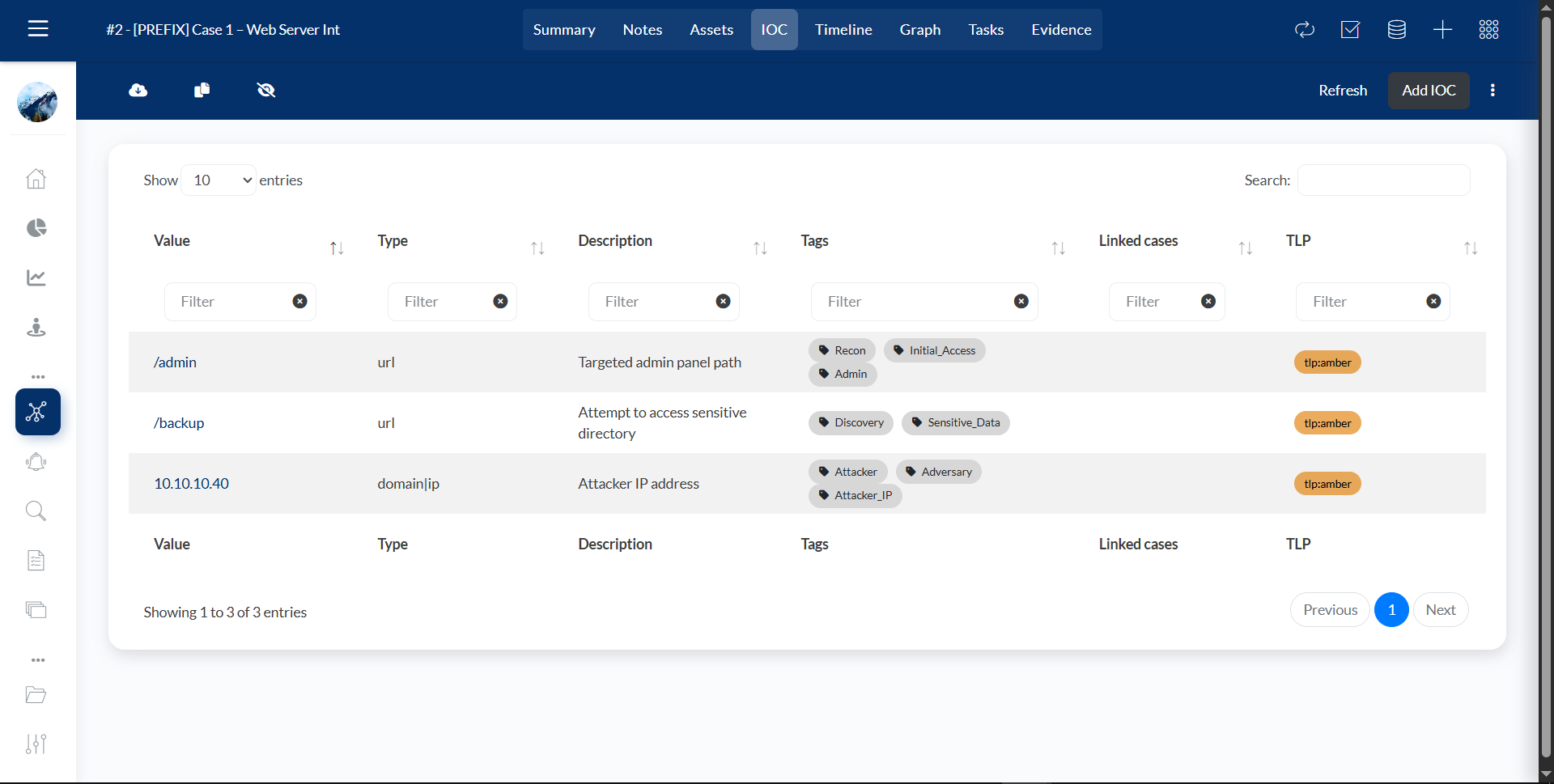
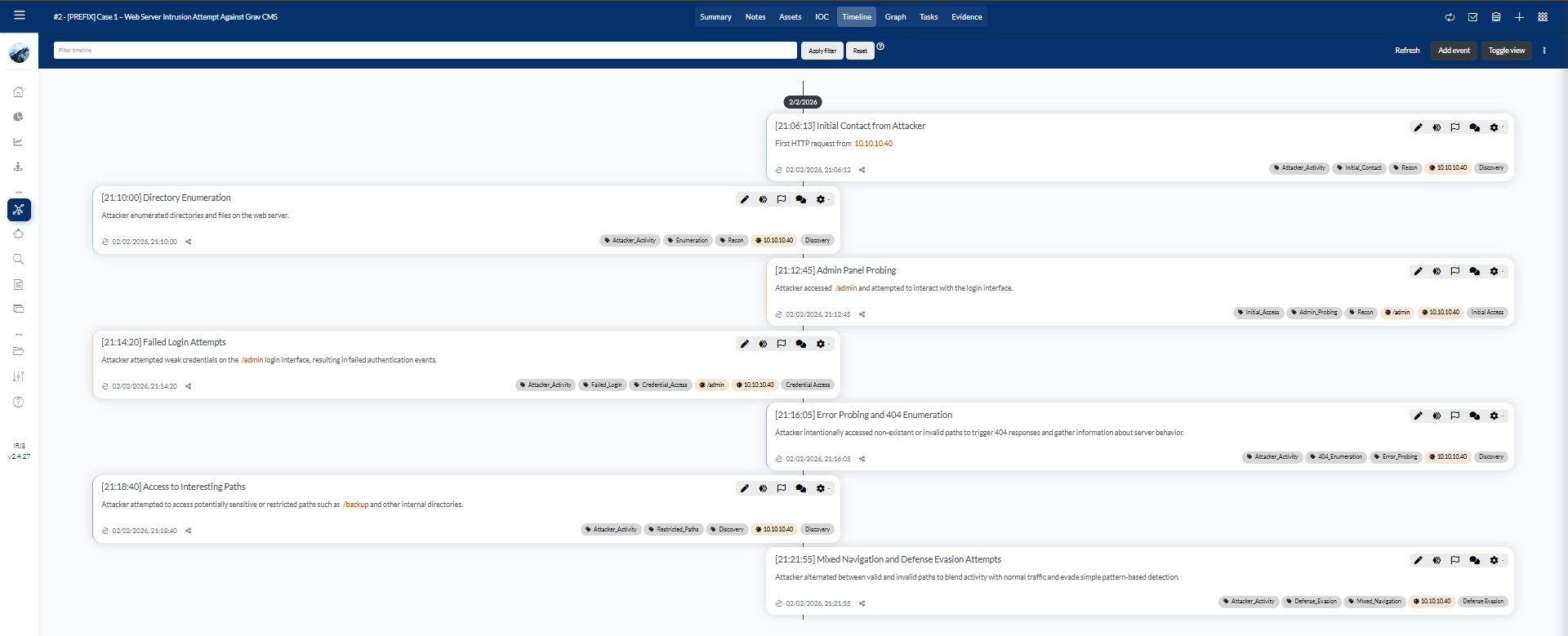
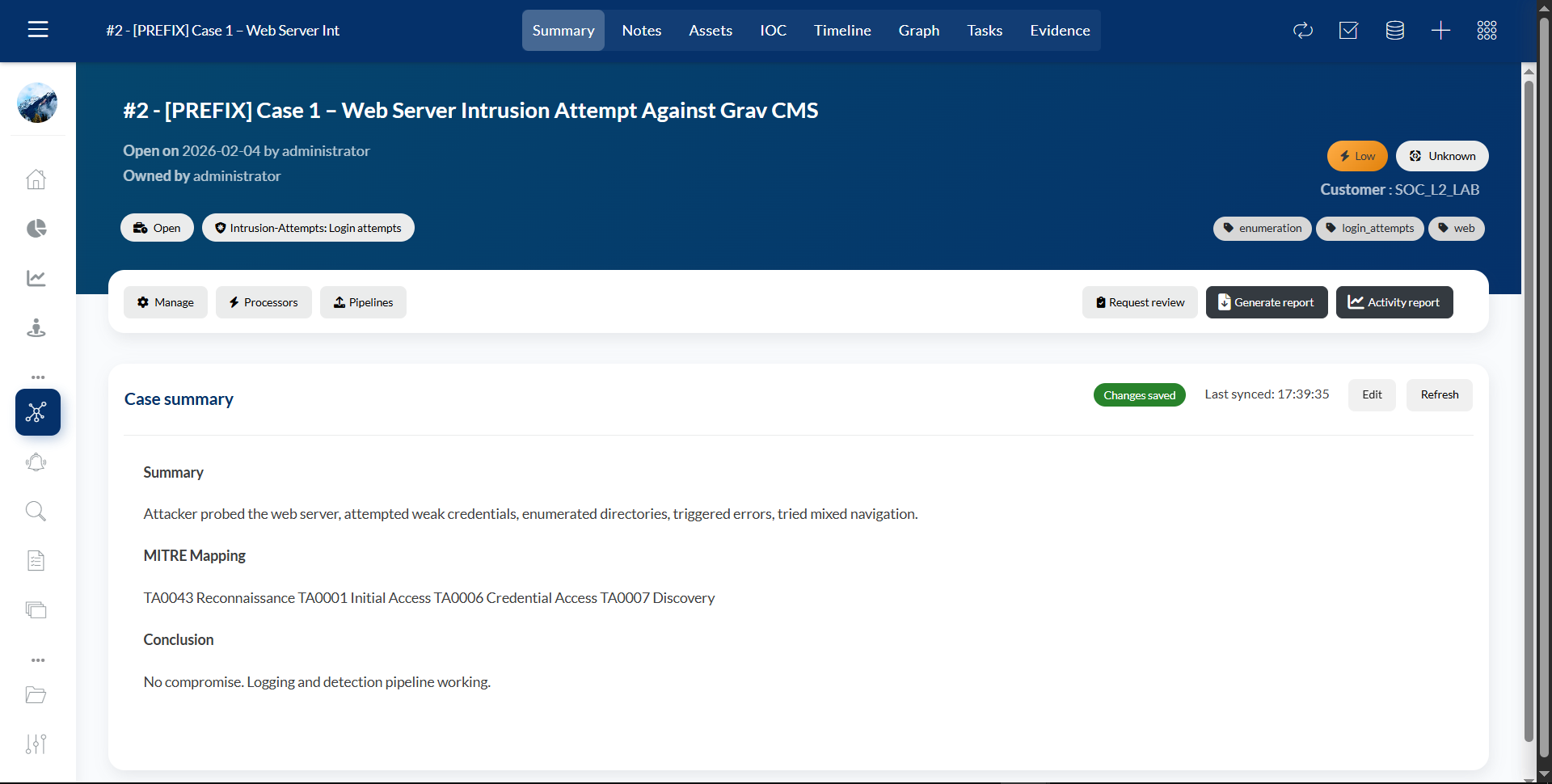
The attacker performed reconnaissance, directory enumeration, admin panel probing, and weak credential attempts. No compromise occurred. Wazuh successfully detected the activity, and DFIR‑IRIS was used to document the investigation.